Adobe has not confirmed it. The only primary source is a cybersecurity analyst account on X. But the technical details circulating about the alleged April 2026 Adobe breach are detailed enough — and the attack methodology specific enough — that compliance officers should treat it as a live case study whether or not Adobe ultimately acknowledges the incident.
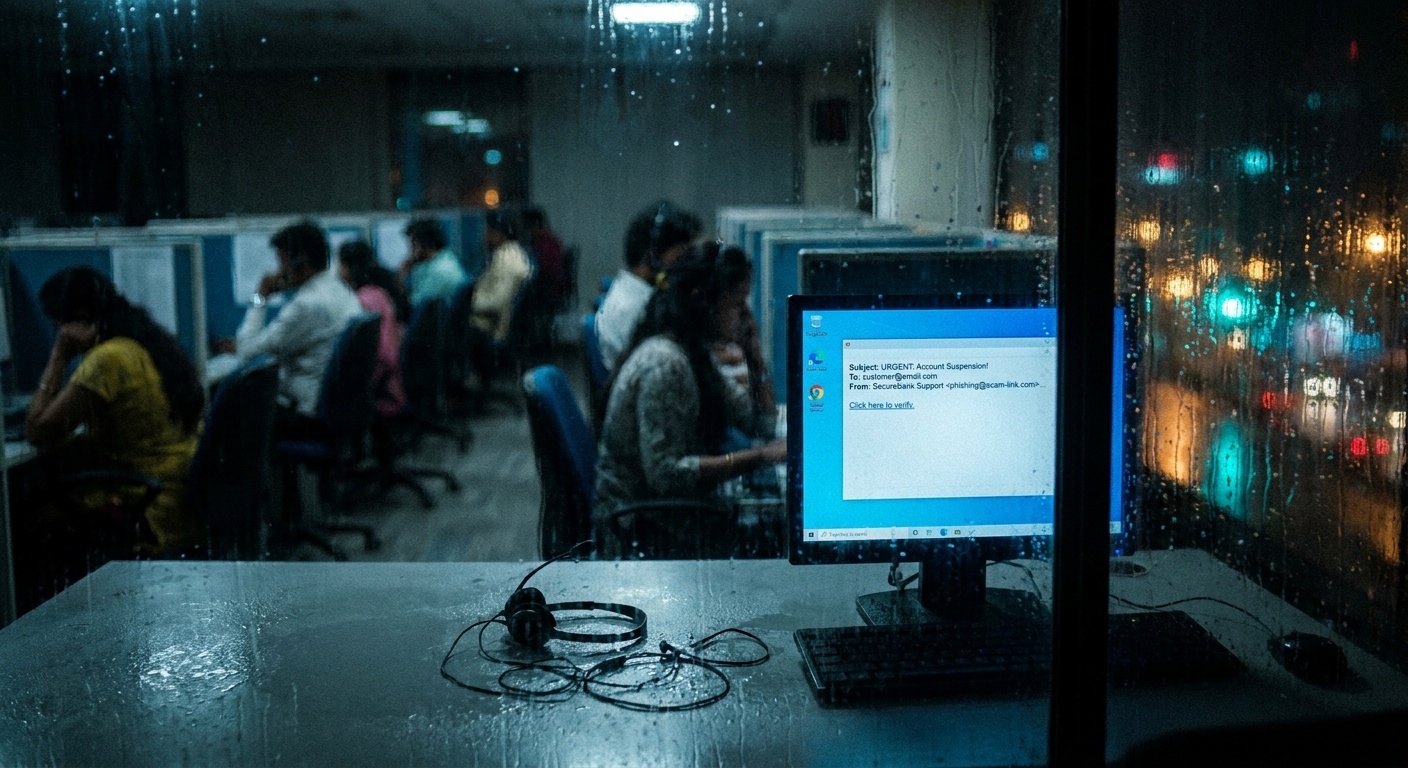
A threat actor identified as “Mr. Raccoon” claims to have exfiltrated approximately 13 million customer support tickets, 15,000 employee records, internal company documents, and the entirety of Adobe’s HackerOne bug bounty program submissions. The alleged method of entry was not a zero-day vulnerability in Adobe’s infrastructure. It was not a nation-state-level intrusion. It was a phishing email sent to an employee at an Indian Business Process Outsourcing company that Adobe had contracted to handle customer support operations.
From there, the attacker reportedly used a compromised workstation and manager-level credentials to access 13 million records without triggering any apparent detection controls.
What Was Allegedly Taken
According to reports from CyberSecurityNews, CyberPress, and Security Online, the exfiltrated data allegedly includes:
- Approximately 13 million customer support tickets containing personal data, issue descriptions, and potentially authentication details shared during support interactions
- 15,000 Adobe employee records
- Internal company documents, scope unknown
- All of Adobe’s HackerOne bug bounty program submissions — including unpatched vulnerability reports
That last item deserves particular attention. If accurate, it means the attacker now has a detailed roadmap of known, unresolved vulnerabilities in Adobe’s products as reported by the security research community. HackerOne submissions are typically embargoed while companies work on patches. Exposure of that database creates direct secondary risk: threat actors can reference disclosed-but-unpatched vulnerabilities for targeted attacks before Adobe can deploy fixes.
Adobe has neither confirmed nor denied the breach as of this writing. The company has not issued a statement, and no official notification has been sent to customers or regulators.
The BPO Attack Surface
Business Process Outsourcing firms represent one of the most systematically underexamined attack surfaces in enterprise security and compliance. Large organizations routinely contract BPO companies — often located in India, the Philippines, Eastern Europe, or Latin America — to handle customer support, data entry, claims processing, and other labor-intensive functions. These relationships are operationally necessary. They are also compliance liabilities that most organizations address inadequately.
The attack methodology described in the Adobe case follows a well-documented pattern:
- Identify the BPO contractor providing customer support services to a high-value target
- Phish a BPO employee — a significantly easier task than targeting a hardened enterprise directly
- Use the compromised BPO account to access the data the BPO was authorized to handle on behalf of the enterprise
- Escalate within the BPO environment to manager-level credentials with broader access
- Exfiltrate at scale
The critical compliance failure is not that an employee was phished. Phishing is a persistent and evolving threat and no organization achieves zero successful phishes indefinitely. The failure is what that single phished account was able to access.
Regulatory Exposure: CCPA, GDPR, and State Privacy Laws
Adobe is headquartered in California, making the California Consumer Privacy Act and the California Privacy Rights Act directly applicable. Under CCPA/CPRA, Adobe is the business and the BPO firm is a service provider — a formal relationship that carries specific contractual requirements.
CPRA Service Provider Obligations (Civil Code §1798.100 et seq.)
Businesses that share personal data with service providers must:
- Enter into a written contract specifying the purpose of the processing
- Prohibit the service provider from retaining, using, or disclosing personal data outside the scope of the contract
- Require the service provider to delete or return personal data upon termination
- Include audit rights and compliance verification mechanisms
If Adobe’s contract with its BPO firm did not include these terms, Adobe faces liability for failing to ensure adequate service provider controls. If the contract included the terms but the BPO failed to implement them, Adobe may face liability regardless if it did not exercise its audit rights to verify compliance.
GDPR (for European data subjects)
Adobe processes data from EU residents, making GDPR Article 28 — which governs processor agreements — applicable to Adobe’s relationship with its BPO contractor. Article 28(3) requires a written contract binding the processor to process data only on documented instructions and to implement appropriate technical and organizational security measures.
Article 28(3)(h) specifically requires that processors “make available to the controller all information necessary to demonstrate compliance with the obligations laid down in this Article” and allow for audits.
The question regulators will ask: did Adobe conduct regular audits of its BPO contractor’s security posture? And if so, did those audits surface the absence of controls that would have prevented a phished employee from exporting 13 million records?
The Privileged Access Problem
What makes the Adobe breach allegation particularly illustrative is the escalation path: a compromised employee account was upgraded to manager-level credentials, which then provided access broad enough to pull 13 million records.
This access pattern indicates systemic failures in privileged access management within the BPO environment:
Excessive data scope: Support agents — and their managers — should only have access to the specific customer records relevant to active support cases. Access to 13 million historical tickets suggests an access model built around operational convenience rather than data minimization.
No anomaly detection on bulk exports: A single session extracting millions of records is an anomalous data access event. Well-configured Data Loss Prevention systems and User and Entity Behavior Analytics tools should flag bulk exports of this volume regardless of the credentials used.
Insufficient MFA on privileged accounts: If manager-level credentials were accessible from a compromised workstation without a second authentication factor, the BPO’s security controls were insufficient for the sensitivity of the data they were handling.
Credential elevation from a phished account: The ability to move from a standard employee account to manager credentials via social engineering or lateral movement suggests inadequate controls on privilege escalation within the BPO environment.
The HackerOne Data: A Compounding Risk
The alleged exfiltration of HackerOne bug bounty submissions represents a secondary compliance and security risk that extends beyond the breach itself.
Bug bounty programs depend on responsible disclosure agreements between security researchers and the target organization. When a researcher submits a vulnerability, they disclose it under the expectation that the organization will remediate it before the vulnerability becomes public. Adobe’s HackerOne program would contain reports of vulnerabilities in Acrobat, Creative Cloud, Adobe Experience Manager, and other widely deployed software products.
If that submission database has been stolen, organizations deploying Adobe software face a material increase in exploitation risk for vulnerabilities that Adobe may still be in the process of patching. Compliance programs with asset inventories and vulnerability management programs should assess their Adobe product exposure and prioritize patching cadences accordingly.
What This Means for Third-Party Risk Programs
The Adobe case illustrates a gap that exists in most enterprise third-party risk programs: the focus on direct vendors while inadequately addressing the vendor’s vendors — often called fourth-party or Nth-party risk.
An organization may perform extensive due diligence on a BPO firm’s security posture: reviewing SOC 2 reports, conducting questionnaires, verifying certifications. But if that BPO firm itself uses subcontractors, offshore facilities, or shared infrastructure — and most do — the security review may not extend to those downstream parties.
Key questions for compliance and risk teams:
- Does your third-party risk program include contractual requirements for subcontractor security standards?
- Do your service provider agreements require notification when a subcontractor will have access to your data?
- Does your audit right extend to subcontractors, or only to the primary contractor?
- Have you mapped which of your service providers operate in environments where your data could be accessed via a compromised BPO workstation?
Compliance Checklist: BPO and Support Operations Data
Contractual requirements:
- Written service provider agreement meeting CCPA §1798.100 and GDPR Article 28 requirements
- Explicit prohibition on subcontracting access to personal data without prior written consent
- Data retention and deletion obligations with verification mechanisms
- Mandatory notification requirements for security incidents affecting your data
Access controls:
- Require MFA for all BPO employee access to production data environments
- Enforce least-privilege — support agents should access only data necessary for the specific ticket or case
- Prohibit bulk data export from support platforms without explicit authorization
- Implement role-based access control that expires when support cases close
Monitoring and detection:
- Deploy anomaly detection capable of flagging unusual export volumes from BPO accounts
- Log all data access events, including who accessed what and when
- Require BPO contractors to provide access logs on request or on a regular cadence
Audit program:
- Conduct annual security audits of BPO contractors with access to significant personal data volumes
- Extend audit scope to include physical security of offshore support centers
- Review subcontractor arrangements and apply equivalent security standards downstream
Incident response:
- Require BPO contractors to notify you within 24-48 hours of any detected security incident
- Maintain an incident response contact chain that reaches BPO security teams directly
- Preserve the right to conduct forensic investigation of BPO environments in the event of a breach
Conclusion
The alleged Adobe BPO breach — confirmed or not — describes an attack model that is being actively used against enterprises worldwide. Outsourcing customer support does not outsource the compliance obligation to protect the personal data processed by that support operation. Regulators in California, the EU, and a growing number of US states are increasingly clear on that point.
Organizations that have not extended their third-party risk programs to cover BPO environments with access to customer personal data should treat this incident as a catalyst for doing so. The attackers already understand that the path to enterprise data often runs through the enterprise’s contractors. Compliance programs need to catch up.
This article is provided for informational purposes only and does not constitute legal advice. Organizations should consult qualified legal counsel regarding their specific compliance obligations under applicable data protection law.