On April 13, 2026, Booking.com confirmed that hackers had accessed customer reservation data, exposing names, email addresses, phone numbers, booking details, and private messages exchanged between guests and hotels. The company stated that no financial data was taken — but travelers were already reporting receiving targeted phishing messages with their exact hotel names, arrival dates, and confirmation numbers, delivered via WhatsApp and email, weeks before Booking.com’s official notification went out.
That timing discrepancy is not merely embarrassing. Under the General Data Protection Regulation, it is a potential enforcement trigger.
What Was Exposed
Booking.com confirmed the following categories of data were accessed:
- Full names
- Email addresses
- Phone numbers
- Booking dates and reservation details
- Private messages between guests and hotel properties
- Hotel-specific notes and special requests
Financial data — credit card numbers, payment account details — was reportedly not included. But the exposed data set is precisely the type of high-value, context-rich personal information that social engineering attacks require to succeed. Attackers armed with a traveler’s name, check-in date, hotel name, and phone number can construct highly convincing impersonation campaigns. Many victims already fell for exactly that before Booking.com notified them the breach had occurred.
The GDPR Notification Question
GDPR Article 33 requires data controllers to notify the relevant supervisory authority of a personal data breach within 72 hours of becoming aware of it. Article 34 requires notification to affected individuals “without undue delay” when the breach is likely to result in a high risk to their rights and freedoms.
This breach puts both provisions in question.
Travelers were receiving scam messages using real reservation data well before Booking.com’s April 12 notification — suggesting the breach occurred considerably earlier. Security researchers investigating the incident assessed that the attack came through compromised hotel partner accounts, a supply chain vulnerability that Booking.com has known about for years and that has previously been exploited. If Booking.com became aware of the breach days or weeks before notifying customers and authorities, the 72-hour clock had already expired.
Booking.com’s registered main establishment in the EU is in the Netherlands, making the Dutch Data Protection Authority (Autoriteit Persoonsgegevens, or AP) its lead supervisory authority under GDPR’s one-stop-shop mechanism.
A Repeat Offender Profile
What makes this incident particularly significant from a compliance standpoint is that it is not Booking.com’s first GDPR breach notification failure — and the Dutch DPA has already penalized the company for exactly this type of lapse.
In 2020, Booking.com suffered a data breach in which fraudsters convinced hotel employees to hand over guest reservation data. Booking.com took 22 days to report the breach to the AP — a full 20 days beyond the 72-hour mandatory window. In 2021, the AP fined the company €475,000 for that delayed notification.
A supervisory authority considering penalties for a second breach with a second potential notification delay will treat prior enforcement history as an aggravating factor. GDPR’s tiered penalty structure under Article 83 permits fines of up to €20 million or 4% of total worldwide annual turnover — whichever is higher. Booking Holdings, Booking.com’s parent company, reported revenues of over $20 billion in 2025. Four percent of global turnover would represent a fine in the range of $800 million.
Whether regulators pursue that ceiling depends on the facts: when Booking.com first became aware, what remediation steps were taken, what internal processes failed, and whether the failure to notify promptly was systemic or situational. The pattern is what makes this difficult to explain away.
The Supply Chain Attack Vector
Security researchers attribute the breach to compromised hotel partner accounts — specifically, credentials belonging to hotel staff who use Booking.com’s internal extranet to manage reservations. This is not a new attack surface. Social engineering campaigns targeting hotel employees have been a documented threat against Booking.com’s platform since at least 2023.
The compliance question here is not whether an external threat actor succeeded. Sophisticated adversaries breach even well-defended organizations. The compliance question is whether Booking.com had adequate controls in place to detect, limit, and respond to a known, documented, previously exploited attack vector.
GDPR’s accountability principle under Article 5(2) requires that controllers be able to demonstrate compliance with data protection principles — including security appropriate to the risk. If a company has experienced a supply chain breach through hotel partner credentials, been fined for inadequate response, and then suffered the same class of attack a second time, demonstrating that appropriate technical and organizational measures were implemented becomes a significant evidentiary challenge.
Key areas regulators will examine:
- Multi-factor authentication for partner accounts: Was MFA mandatory for hotel extranet users? Was it enforced?
- Access scope and data minimization: Did hotel staff accounts have access to guest personal data beyond what was operationally necessary?
- Anomaly detection: Were there monitoring controls capable of detecting unusual data access or export patterns from partner accounts?
- Incident response timelines: When was anomalous activity first detected? When was a breach determination made? When were authorities and individuals notified?
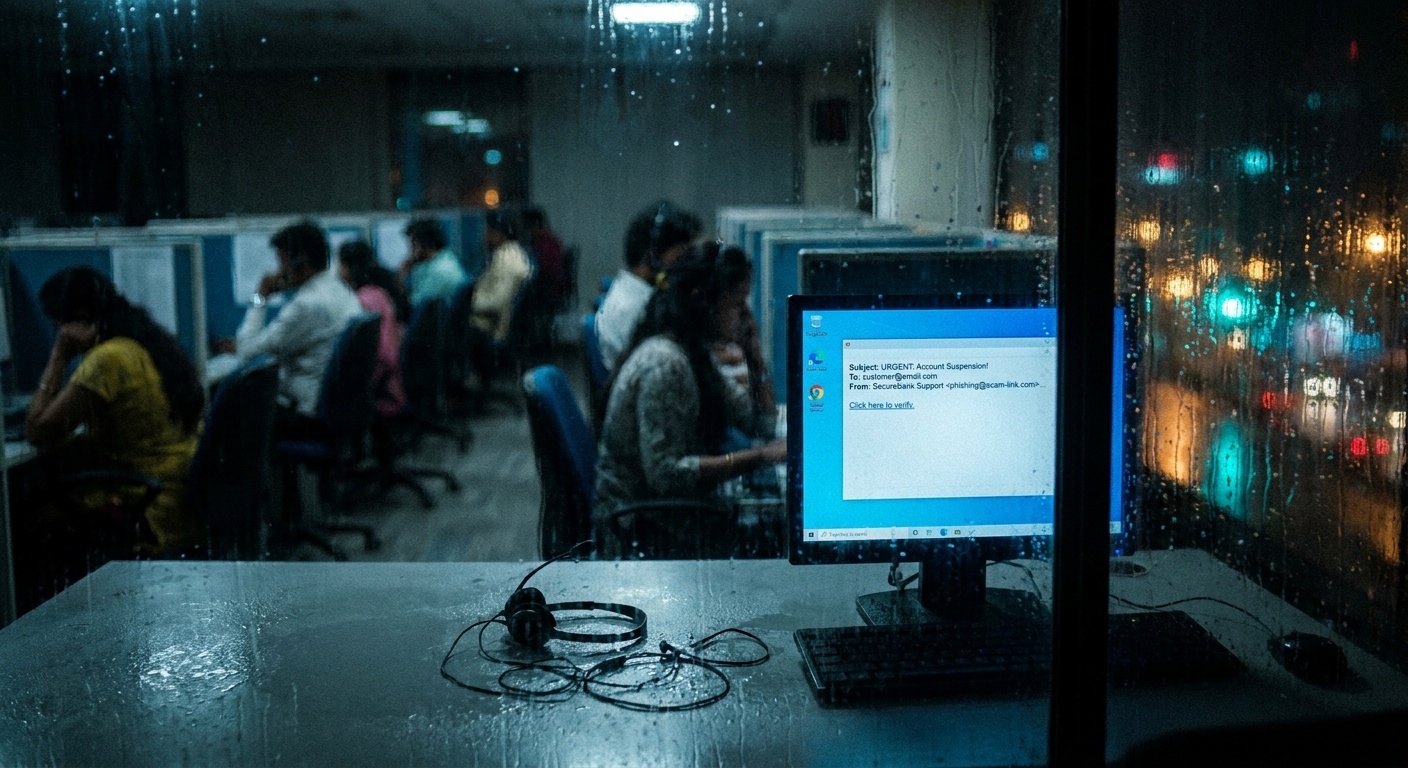
What the Phishing Activity Tells Us
The rapid emergence of targeted phishing campaigns using stolen reservation data reveals something important about how this breach was exploited. The attackers did not simply exfiltrate data and sit on it. They used it immediately for financial fraud, contacting travelers with impersonation messages mimicking Booking.com’s communications style.
This confirms that the breach represented a “high risk” to affected individuals’ rights and freedoms — the precise threshold that triggers mandatory notification to individuals under GDPR Article 34. The fact that travelers were being targeted before Booking.com notified them of the breach means that the company’s failure to notify promptly may have directly contributed to harm to its customers.
That harm-causation chain is meaningful in any regulatory enforcement assessment and in any civil litigation that follows.
Regulatory and Legal Exposure
Beyond the AP, this breach carries exposure on multiple fronts:
EU enforcement: Lead supervisory authority investigation, potential fines, possible requirement to appoint a representative or undergo audit.
UK GDPR: Booking.com also operates under UK GDPR following Brexit. The Information Commissioner’s Office may open its own inquiry if UK residents were affected.
Civil litigation: Class action claims are possible in jurisdictions where affected individuals can seek compensation for material or non-material damage under GDPR Article 82.
Reputational damage: In an industry built on trust and personal travel data, a repeat breach with a repeat notification failure carries significant brand risk.
Compliance Lessons and Checklist
Organizations managing large volumes of consumer personal data through partner networks should treat this incident as a direct case study in what systemic third-party risk failure looks like at scale.
Third-party access controls:
- Enforce MFA for all partner and vendor accounts with access to personal data
- Apply least-privilege access — partners should access only the data required for their specific function
- Conduct periodic access reviews and promptly revoke credentials for inactive or departing hotel partners
- Log all partner account activity and review anomalous access patterns
Incident detection and response:
- Establish clear criteria for what constitutes “awareness” of a breach that starts the GDPR 72-hour clock
- Assign ownership of breach notification obligations to a specific role with authority to escalate immediately
- Maintain documented incident response playbooks and test them regularly
- Do not wait for breach confirmation before notifying regulators — notify based on reasonable grounds to believe a breach has occurred
Notification readiness:
- Maintain up-to-date records of which supervisory authority is lead authority and what their preferred notification channels are
- Pre-draft notification templates for high-risk data categories
- Ensure data subject notification processes can be activated quickly and at scale
Prior enforcement remediation:
- Document what changes were implemented following prior enforcement actions
- Verify those controls were actually deployed and working, not just planned
- Prepare to demonstrate remediation steps to regulators in any subsequent investigation
Conclusion
Booking.com’s April 2026 breach is not simply a data security incident. It is a test of whether five years of GDPR enforcement have produced meaningful behavioral change at a company that has already been penalized for the same category of failure.
The 72-hour notification window exists because early warning is the most effective mitigation available to breach victims. Travelers who were phished using their own reservation data before Booking.com told them anything had happened were denied that protection. Regulators will ask why — and the answers will determine whether this breach results in a modest fine or a headline-making penalty that resets how the travel industry approaches partner account security.
For compliance officers managing large partner ecosystems, the lesson is already clear: if a known attack vector is exploited once, investing in controls to prevent recurrence is not optional. It is the difference between a defensible incident and an indefensible pattern.
This article is provided for informational purposes only and does not constitute legal advice. Organizations should consult qualified legal counsel regarding their specific compliance obligations under applicable data protection law.