The May 2026 Instructure Canvas breach exposed names, institutional email addresses, student ID numbers, and private messages for an estimated 275 million records across 8,809 institutions in more than 50 countries. The breach narrative is covered separately. This piece focuses on the part that matters for general counsel, compliance officers, district attorneys, and school board members: who has to notify whom, on what clock, with what data — and what to do when the vendor cannot give you tenant-specific scope information for weeks.
The short version: the notification burden sits on the institutions, not on Instructure. Your regulatory clocks started May 1, 2026. You will be expected to notify before Instructure can tell you exactly what was in your tenant. That is the operating reality of this incident.
The Compliance Hinge: Notification Burden Sits With the School
Under FERPA, schools remain responsible for protecting student records even when those records sit in a platform the school doesn’t operate. The same allocation of responsibility shows up in COPPA, in state student privacy statutes, and in most institutional Data Processing Agreements with EdTech vendors. Vendors are processors. Schools are controllers. Controllers notify.
Practically, that means:
- Instructure is not the entity that owes notice to your students, parents, or state AG.
- Instructure’s e-discovery review timeline — weeks to months, per their own public statements — is not a defense to your notification deadlines.
- Your insurer’s notification trigger is awareness of incident, not confirmation of scope. That clock started May 1.
This is the structural feature of EdTech that the next year of post-breach litigation will be about. For now, every affected institution needs to act as if its own notification clock is running, because it is.
The Framework-by-Framework Matrix
FERPA (U.S. — Family Educational Rights and Privacy Act)
Who’s covered: Any U.S. educational institution receiving federal funds. Essentially all K-12 districts and virtually all higher education institutions.
What’s triggered: Unauthorized disclosure of “education records” — which the Department of Education interprets broadly to include not just grades and transcripts, but identifying information tied to a student’s educational experience. Student ID numbers plus name plus institutional email plus course messaging content all qualify.
Notification timeline: FERPA has no statutory breach-notification deadline analogous to HIPAA’s 60-day rule. However, DOE guidance increasingly expects “prompt” notification to affected students and parents. Failure to maintain reasonable safeguards can result in loss of federal funding — the primary FERPA enforcement teeth. The DOE Office of the Chief Privacy Officer (Student Privacy Policy Office) is the relevant inquiry body and has been increasingly active on EdTech-vendor breaches.
Action item: Document the safeguards you had in place with Instructure — Data Processing Agreement, security addenda, audit reports — document the timeline of your response, and prepare a FERPA-specific notification framework for affected populations.
COPPA (U.S. — Children’s Online Privacy Protection Act)
Who’s covered: Any school or vendor processing data of children under 13. Most K-12 districts. Some higher education pipeline programs.
What’s triggered: The updated COPPA rule took effect April 22, 2026 — nine days before the Canvas exposure window started. The updated rule tightens consent, expands the definition of personal information, and introduces sharper enforcement teeth.
Notification timeline: COPPA does not impose a strict statutory notification deadline on schools directly, but the FTC can pursue per-violation penalties (currently up to $51,744 per violation). “Per violation” can be interpreted per-child for systemic failures. The FTC’s 2026 enforcement posture has been markedly more aggressive on EdTech.
Math that should concern you: Affected K-12 systems include LAUSD, Chicago Public Schools, Miami-Dade, Clark County (Las Vegas), Houston ISD, the entire Hawaii Department of Education, Boston Public Schools, Detroit, Dallas ISD, and dozens more. The combined under-13 student populations in those systems exceed several million. Schools cannot offload this to Instructure as a vendor problem — schools are the COPPA-regulated entities for their own student populations.
Action item: Identify whether your district uses Canvas with any under-13 population. If yes, COPPA is in play and parental notification is structurally different from standard FERPA notice — it needs to address the parent as the rights-holder, not the child.
HIPAA (U.S. — Health Insurance Portability and Accountability Act)
Who’s covered: Teaching hospitals, medical schools, university health systems, and any institution that used Canvas for clinical training programs where PHI may have flowed through course content or messaging.
What’s triggered: Possible PHI exposure depending on what specific institutions ran through Canvas. Trend Micro’s analysis flagged Weill Cornell Medical College, the University of Nebraska Medical Center, and several Brazilian hospital systems as HIPAA-relevant entities on the affected list.
Notification timeline: HIPAA Breach Notification Rule — 60 days from discovery for breaches affecting 500 or more individuals, plus HHS Office for Civil Rights notification and media notification in the affected state.
Action item: If any clinical training, residency, or PHI-adjacent content flowed through your Canvas instance, treat this as a potential HIPAA breach until forensics can confirm otherwise. 60 days from May 1 is June 30, 2026.
State Student Privacy Statutes (U.S. — Approximately 130 Frameworks)
Who’s covered: Varies. Roughly 130 state-level student privacy statutes across the 50 states and D.C., with the strongest enforcement teeth in California (SOPIPA, CCPA, CPRA), Colorado, Illinois (SOPPA), Virginia (CDPA), New York (Education Law §2-d), Connecticut, and Texas.
What’s triggered: Most state student privacy frameworks contain notification triggers that activate independently of FERPA, often with shorter timelines and broader definitions of personal information.
Selected notification timelines:
- California (AG notification under CCPA breach): “Without unreasonable delay” plus state AG notification if 500 or more residents affected.
- Illinois (SOPPA): District must notify within 30 days of vendor notification.
- New York (Ed Law §2-d): 60 days, with specific parent notification language requirements.
- Connecticut (Public Act 16-189): Vendors must notify schools “as soon as possible,” and schools must then notify parents “without unreasonable delay.”
- Colorado (HB 16-1423): 30-day district notification to parents after vendor disclosure.
- Texas (SB 820 / Chapter 32 Ed Code): Notification “as soon as practicable” with AG involvement for large breaches.
Action item: Pull every state in which your students reside — this is broader than your campus location; out-of-state students count. Map each to its student privacy framework. Build a notification calendar with the earliest deadline as the controlling one.
GDPR (EU)
Who’s covered: Any institution holding EU data subject records. This includes EU students enrolled at U.S. institutions, U.S. study-abroad participants whose records flowed through Canvas, and the European institutions on the affected list.
What’s triggered: Articles 33 and 34 obligations — supervisory authority notification and data subject notification.
Notification timeline: 72 hours for supervisory authority notification from awareness. The May 1 clock started running 72 hours later on May 4, 2026.
Action item: If you have any EU data subject exposure, you are likely already past the strict 72-hour window. Document why notification was delayed — forensic uncertainty is an accepted reason if properly documented — prepare an Article 33 notification, and consult counsel on whether Article 34 individual notification thresholds are met.
UK, Australia, and Other Jurisdictions
UK ICO: 72-hour notification under UK GDPR. 125 named UK institutions on the affected list. Online Safety Act framework adds complexity for K-12 and under-18 populations.
Australia (Notifiable Data Breaches scheme): 30-day assessment window, then “as soon as practicable” notification. 138 named Australian institutions. Several Australian state education ministries are on the list and have already preemptively disconnected Canvas.
Singapore (PDPA): 72-hour notification to the Personal Data Protection Commission for breaches affecting 500 or more individuals.
Canada (PIPEDA plus provincial frameworks): “As soon as feasible” notification, with provincial variation — Quebec’s Law 25 is the strictest.
The Vendor Side: What Your DPA Says vs. What You Need
If you have a Data Processing Agreement with Instructure — and you do — now is the moment to read it. Specifically:
Notification timing clauses. What is the contractual obligation on Instructure to notify you of a security incident? In hours? Days? “Without undue delay”? The looser the language, the weaker your position when the forensic report lands months from now.
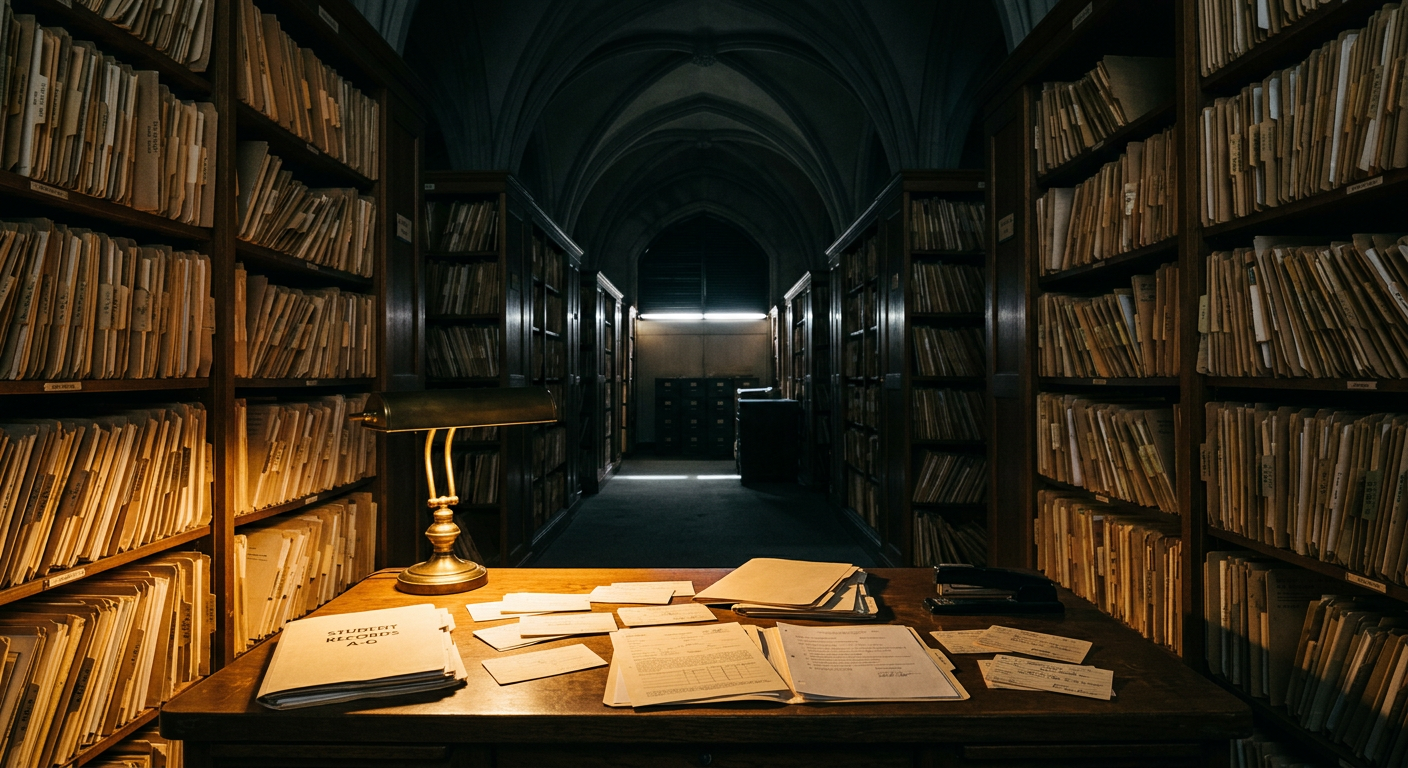
Scope-of-disclosure clauses. Does the contract obligate Instructure to provide tenant-specific scope information — i.e., which of your specific records were accessed — within a defined timeline? Most EdTech DPAs do not. This is the single most important contract clause for breach response and almost no school district negotiates it.
Indemnification. Does Instructure indemnify you for breach-related costs? Subject to what caps? Most EdTech vendor indemnification is capped at 12 months of fees paid, which for a single school district is materially less than the actual cost of a breach response.
Audit rights. Do you have contractual audit rights or only SOC 2 reliance? In the post-breach forensic conversation, the difference is significant.
Sub-processor disclosure. When Instructure brought in CrowdStrike and an e-discovery vendor to respond to this incident, your data started being processed by entities you didn’t authorize. Most DPAs allow this. They shouldn’t.
For institutions whose Instructure contracts renew in the next 6–12 months, this is the renegotiation leverage moment. Document every gap now while the operational pain is fresh.
What Counsel Should Do This Week
Days 1–3 (if not already done)
- Engage outside cyber counsel under privilege. Anything not privileged is discoverable.
- Notify your cyber insurance carrier. Most policies trigger on awareness, and most require written notice within 30 days or less.
- Stand up a defined incident response team with named owners for communications, legal, IT/security, and regulatory.
- Issue informal community notification — a short note from a named leader (provost, superintendent, president) explaining what is known, what is not, and what the institution is doing. Do not wait for the forensic report.
Days 4–14
- Build the notification matrix — every framework, every deadline, every population. Use the matrix above as a starting template.
- Press Instructure for a tenant-specific scope letter. Demand a commitment date. “Several weeks” is not a date.
- Rotate every Canvas API token, OAuth integration credential, and SSO trust relationship from the exposure window. Anything that authenticated to Canvas between April 30 and May 7 is potentially exposed.
- Document everything. Every meeting, every decision, every external communication. State AG inquiries are coming and good records are your defense.
Days 14–60
- File required notifications under the controlling-deadline framework. The strictest applicable framework drives the timeline.
- Prepare board-level briefings. In writing. On the record. This protects directors and trustees from individual liability claims.
- Begin data minimization review. What student data is flowing into Canvas that doesn’t need to be there? Less data equals less liability next time. There will be a next time.
- Re-read your DPA renewal calendar and stage your renegotiation strategy.
Days 60–180
- Final notifications based on Instructure’s tenant-specific scope letter, whenever it arrives.
- Documented post-incident review submitted to the board.
- Policy updates: incident response plan, vendor risk management policy, data classification policy, data retention schedule.
The DPA Negotiation Lessons That Apply Industry-Wide
This breach will drive a wave of EdTech DPA renegotiations through the back half of 2026. The lessons generalize:
Notification timing must be measured in hours, not “without undue delay.” 24 or 48 hours from vendor awareness, with defined contact methods and escalation paths.
Tenant-specific scope information must have a contractual SLA. “We will provide preliminary scope within 30 days and final scope within 90 days” is far better than the typical “as soon as practicable.”
Sub-processor changes require advance notice and opt-out rights. When Instructure brought in third-party forensic and e-discovery vendors, your data was being processed by entities you did not authorize. Most DPAs allow this. They shouldn’t.
Indemnification caps must be sized to realistic breach cost, not annual fees. A $50K annual contract should not cap indemnification at $50K when the realistic breach cost to a mid-sized district is $2–5 million.
Audit rights should be real, not theoretical. SOC 2 reliance is not sufficient post-Canvas, post-PowerSchool, post-Illuminate.
Data minimization should be contractual. Vendors should be obligated to delete data fields the institution is not actively using — not allowed to retain everything indefinitely.
Multi-tenant architecture disclosures. Vendors should be obligated to disclose tier-sharing between free and paid customers running on the same back-end infrastructure. The Canvas free-tier exposure story would not have happened without that architectural blurring.
The Larger Compliance Posture Question
The Canvas breach is the third large EdTech-vendor incident in 18 months — PowerSchool and Illuminate preceded it. The pattern is consistent: a single vendor compromise affects thousands of institutions, the vendor controls the forensic timeline, the institutions carry the notification burden, and the regulatory framework places liability on the regulated entity (the school) even though the technical failure occurred at the platform layer.
For school counsel, compliance officers, and risk managers, the strategic implication is straightforward and uncomfortable:
You cannot procurement your way out of breach liability. Consolidating onto a single LMS, SIS, or student services platform makes financial and operational sense, but it does not transfer compliance obligations to the vendor. It concentrates them. The procurement decision that simplified your stack also widened your blast radius.
The institutions that come out of the Canvas breach in the best legal position will be the ones that:
- Had clear written DPAs with measurable notification SLAs
- Had vendor risk management policies that contemplated tier-sharing and supply chain failures
- Had practiced incident response plans that did not depend on the vendor as the lead actor
- Had documented data minimization practices to limit blast radius
- Had board-level briefings on the record before the breach happened
For most institutions, that work begins now. Not after the next breach. Not after the Instructure forensic report. Now.
This article is provided for informational purposes only and does not constitute legal advice. Institutions with specific questions about their notification obligations following the Canvas breach should consult qualified legal counsel with expertise in education law, privacy regulation, and cybersecurity incident response.