In the span of a single week — April 1 through April 7, 2026 — five separate class action lawsuits landed in federal courts in California and Texas against Mercor.io Corporation, the AI recruiting startup that disclosed a data breach on March 31. The complaints vary in scope, in named defendants, and in legal ambition. Together, they paint a picture of a company that handled extraordinarily sensitive data — Social Security numbers, identity verification passports, recorded video interviews with AI systems, proprietary source code — while allegedly failing to implement basic security controls that most compliance frameworks consider table stakes.
This article breaks down each known lawsuit, the legal theories in play, and what compliance professionals need to understand about where this is heading.
What Happened: The Breach in 30 Seconds
Mercor connects domain experts — doctors, lawyers, engineers, scientists — with AI labs like OpenAI, Anthropic, and Meta to generate training data for large language models. The company raised a $350 million Series C in October 2025 at a $10 billion valuation and was reportedly on pace to exceed $1 billion in annualized revenue before the breach.
On March 27, 2026, a threat actor group called TeamPCP compromised the PyPI publishing credentials for LiteLLM, a widely used open-source Python library maintained by BerriAI (a Y Combinator-backed startup). TeamPCP published two malicious versions — 1.82.7 and 1.82.8 — containing a three-stage backdoor designed to harvest authentication credentials and API keys. The poisoned packages were live for roughly 40 minutes before being detected and quarantined.
That 40-minute window was enough. LiteLLM is estimated to be present in 36% of cloud environments and is downloaded millions of times daily. Thousands of systems pulled the compromised packages automatically, and the stolen credentials were used to pivot deeper into victim environments.
Mercor confirmed on March 31 that it was “one of thousands of companies” affected. But the extortion group Lapsus$, which security researchers say partnered with TeamPCP to monetize stolen access, claimed to have exfiltrated approximately four terabytes from Mercor specifically — and began auctioning the data on dark web forums.
The alleged haul: a 211-gigabyte user database, 939 gigabytes of platform source code, roughly three terabytes of storage buckets containing video interviews and identity verification passports, TailScale VPN configuration data, internal Slack communications, and ticketing system data.
Meta indefinitely paused all work with Mercor. OpenAI said it was investigating. Anthropic has not publicly commented. Multiple law firms began circling. And then the complaints started landing.
For a deep dive into how the breach connects to the Delve fake compliance scandal and Mercor’s contractor surveillance practices, see our companion analysis: Fake Compliance, Stolen Credentials, and 4 Terabytes of AI Secrets: Inside the Class Action That Connects Mercor, LiteLLM, and Delve.
The Lawsuits: Case by Case
1. Deboni v. Mercor.io Corporation
Case No.: 3:26-cv-02821
Court: U.S. District Court, Northern District of California
Filed: April 1, 2026
Plaintiff’s Counsel: Brian S. Quinn
Named Defendants: Mercor.io Corporation
The Deboni complaint was among the first to hit the docket. Filed the same day as Gill, it establishes the baseline negligence theory that runs through several of the California filings: Mercor collected and stored sensitive personal information from contractors and failed to implement adequate cybersecurity protections, resulting in unauthorized access during the LiteLLM supply chain compromise.
While the full complaint text is not publicly available outside PACER, the docket confirms it was filed as a class action on April 1, the day after Mercor’s public disclosure. It targets Mercor alone — without naming LiteLLM, BerriAI, or Delve as co-defendants — suggesting a straightforward data breach negligence theory focused on Mercor’s own security failures rather than the upstream supply chain.
2. Gill v. Mercor.io Corporation
Case No.: 3:26-cv-02831
Court: U.S. District Court, Northern District of California
Filed: April 1, 2026
Plaintiff: Lisa Gill (Wahiawa, Hawaii)
Plaintiff’s Counsel: Brian S. Quinn, Etienne C. Toussaint
Named Defendants: Mercor.io Corporation
Proposed Class: All U.S. residents whose personal information was accessed or acquired during the breach
The Gill complaint is the most detailed of the California filings and has become the lead case cited in most media coverage. It proposes a nationwide class covering more than 40,000 individuals.
The complaint’s core allegation is that Mercor’s cybersecurity practices fell well below industry standards. Specifically, Gill alleges Mercor failed to:
- Implement multi-factor authentication
- Encrypt sensitive data during storage and transmission
- Limit which employees or systems could access personal information
- Monitor systems for suspicious or anomalous activity
- Rotate passwords regularly to reduce the risk of credential compromise
For compliance professionals, this list reads like a checklist of controls you’d expect any SOC 2 audit to evaluate. The absence of MFA alone — in 2026, for a company handling biometric data and Social Security numbers — is a significant allegation. These aren’t exotic controls. They’re the kind of baseline protections that frameworks like NIST CSF, ISO 27001, and SOC 2 treat as foundational.
The personally identifiable information at issue includes full names, Social Security numbers, and other sensitive data belonging to current and former contractors and customers. Gill alleges she personally lost significant time dealing with the breach consequences and faces an elevated risk of identity theft.
The complaint seeks compensatory damages, consequential damages, statutory damages, nominal damages, punitive damages, and injunctive relief requiring Mercor to improve its security practices.
3. Esson v. Mercor.io Corporation
Case No.: 3:26-cv-02839
Court: U.S. District Court, Northern District of California
Filed: April 1, 2026
Plaintiff: NaTivia Esson
Plaintiff’s Counsel: Strauss Borrelli (Andrew Gunem)
Named Defendants: Mercor.io Corporation
The Esson complaint is the most personal of the filings — and arguably the most effective at establishing the human stakes of the breach.
NaTivia Esson alleges she worked as a contractor for Mercor from March 2025 through March 2026. Each time she received new work through the platform, she submitted a W-9 form containing her personal identifying information. She trusted the company would use reasonable measures to protect it.
That trust, the complaint alleges, was misplaced. The lawsuit states that because of the data breach, Esson anticipates spending considerable amounts of time and money to mitigate her injuries — a framing that establishes concrete, ongoing harm rather than speculative future risk.
The Esson complaint is significant for the litigation trajectory because it establishes a specific factual pattern of repeated, trusting disclosure of PII by a named individual contractor who relied on Mercor’s implicit security assurances over a documented twelve-month period. In class certification proceedings, this kind of representative plaintiff — with clear, documented reliance and ongoing harm — is exactly what courts look for.
Esson’s attorneys at Strauss Borrelli are experienced data breach class action litigators, which suggests this filing was made with a long-term litigation strategy in mind, not simply as an opportunistic first-mover complaint.
4. White and Beltran v. Mercor.io Corp., Delve Technologies, Inc., and Berrie AI Incorporated
Case No.: 6:26-CV-00143-H
Court: U.S. District Court, Northern District of Texas, San Angelo Division
Filed: April 5, 2026 (First Amended Complaint)
Plaintiffs: Heidi L. White and Kristen Beltran, individually and on behalf of all others similarly situated
Named Defendants: Mercor.io Corporation, Delve Technologies Inc. (d/b/a Delve), Berrie AI Incorporated (d/b/a LiteLLM), and John Doe LLM Companies 1-10
This is the big one.
The White and Beltran First Amended Class Action Complaint is the most ambitious filing in the Mercor litigation — and the only one to name multiple defendants across the supply chain. It doesn’t just allege a data breach. It alleges a systemic failure of the trust infrastructure that the AI industry depends on, spanning three categories of misconduct:
The Supply Chain Attack. The complaint details TeamPCP’s compromise of LiteLLM’s PyPI credentials, the injection of malicious backdoors into versions 1.82.7 and 1.82.8, and the subsequent exfiltration of approximately four terabytes from Mercor’s systems.
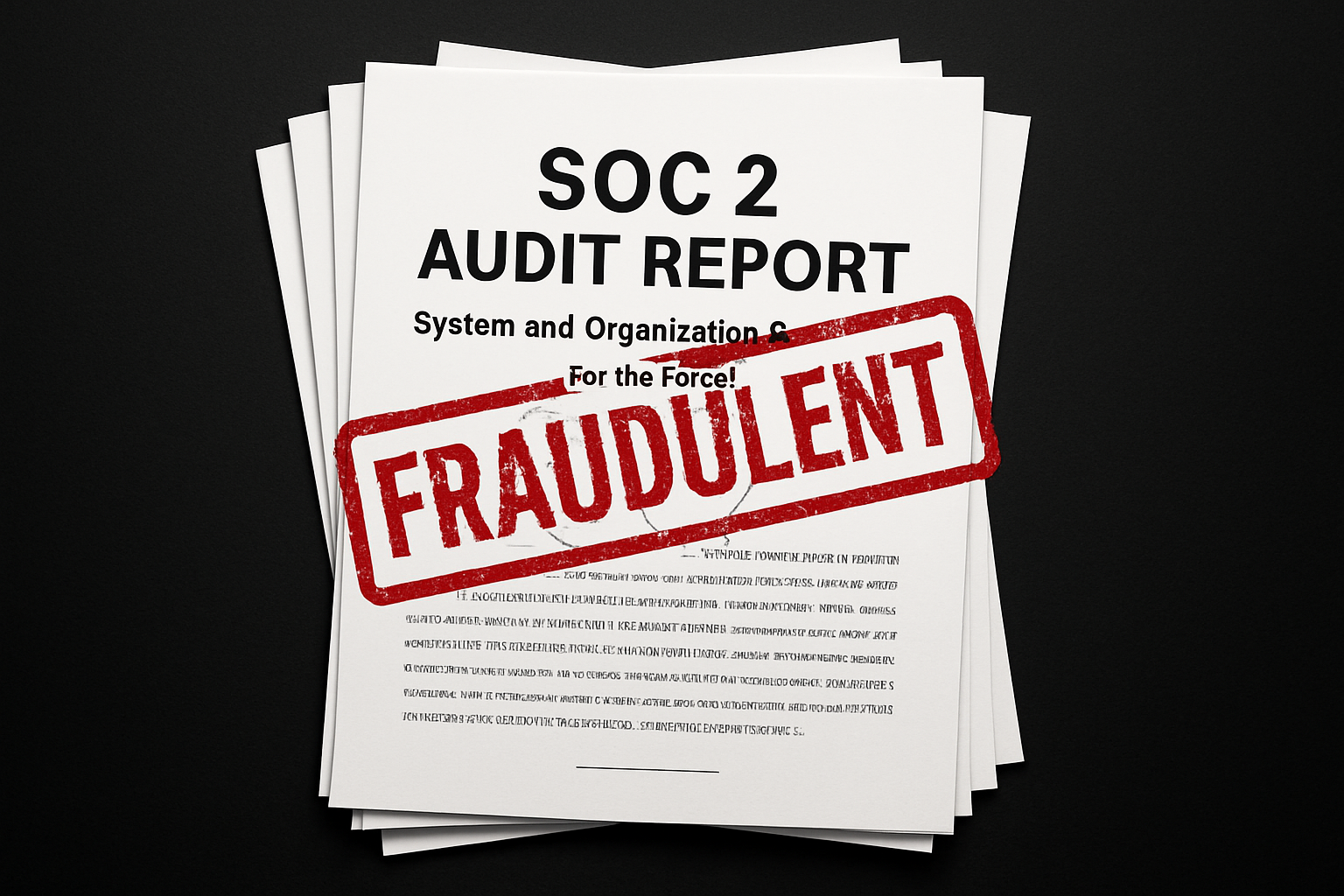
The Fake Compliance Certifications. The complaint alleges that Delve Technologies systematically fabricated compliance certifications for its customers beginning in or around 2023. It cites at least 494 fabricated compliance reports, generated from identical templates with pre-written auditor conclusions prepared before customers provided any evidence of actual compliance. Delve generated fake evidence of board meetings, security tests, and compliance processes that never occurred. LiteLLM obtained its SOC 2 and ISO 27001 certifications through Delve — certifications it then displayed to downstream users like Mercor to represent robust security controls.
The complaint notes that following the breach, LiteLLM severed ties with Delve and announced it would pursue recertification through Vanta — characterizing this remedial action as an implicit acknowledgment that Delve’s certifications were inadequate.
The Contractor Surveillance and LLM Training Data Pipeline. Perhaps most distinctively, the complaint alleges that Mercor required contractors to operate invasive monitoring software called Insightful (formerly Workpuls) that randomly captured screenshots of contractors’ screens during work sessions. These captures allegedly recorded proprietary source code, trade secrets, personal emails, banking information, medical data, and attorney-client privileged communications belonging to third parties.
The complaint then alleges Mercor sold, licensed, or provided this captured data — along with recorded interviews, personal information, and work product — to unnamed “John Doe LLM Companies 1-10” for use in training large language models. The John Doe defendants allegedly knew or should have known that the data included material harvested through invasive surveillance.
The White and Beltran complaint is the first to tie the compliance fraud, the supply chain attack, the contractor surveillance, and the LLM training data pipeline into a unified theory of liability. It also surfaces a striking contractual contradiction: Mercor required contractors to sign agreements prohibiting them from disclosing their employers’ confidential information, while Mercor’s own screen monitoring software was engineered to capture exactly that information from contractors’ screens.
5. The Fifth Filing
Business Insider and TechCrunch have reported that a fifth lawsuit was filed during the same April 1–7 window, also in federal court. The specific case name and docket number have not been independently confirmed in public reporting as of this writing. All five suits seek unspecified monetary damages for violations of data privacy and consumer protection laws.
The Legal Landscape: What’s at Stake
Settlement Benchmarks
For context on the financial exposure, Cornerstone Research published a survey of data breach class action settlements from 2018 through 2021 that found typical payouts ranged from $1 to $5 per class member, with higher amounts for individuals who could document specific financial losses. Some settlements also include non-monetary relief such as credit monitoring services.
With a proposed class of over 40,000 affected individuals, the floor for a modest settlement is relatively low in dollar terms. But Mercor’s situation has several factors that could push outcomes higher: the sensitivity of the exposed data (biometric information, identity documents, SSNs), the company’s $10 billion valuation, the involvement of high-profile AI lab clients, and the parallel Delve scandal adding a layer of systemic negligence that extends beyond a simple security failure.
The MercorClaims.com Factor
An apparent lead-generation website, MercorClaims.com, went live on or around April 1. The site describes itself as providing general informational content about the Mercor data breach, a waitlist for updates, and investigation-intake forms. It explicitly disclaims any attorney-client relationship and states it is not affiliated with Mercor. The site’s terms of service were last updated April 1, 2026.
While the site doesn’t currently route users to any specific law firm, its existence signals that the plaintiff’s bar sees potential for a much larger litigation effort than the five complaints filed so far. Lead-generation sites of this type typically appear when lawyers anticipate significant class certification and expect to need a large pool of documented claimants.
Pre-Existing Legal Exposure
The data breach lawsuits aren’t the only legal headaches for Mercor. The company was already defending against a trade secrets lawsuit filed by Scale AI in September 2025 (Case 3:25-cv-07402, N.D. Cal.), which alleges a former Scale employee stole documents while being recruited by Mercor. Separately, a California employment class action — Cox v. Mercor Io Corporation — was filed in October 2025 in Santa Barbara County Superior Court, accusing Mercor and OpenAI of misclassifying AI trainers as independent contractors and installing intrusive monitoring software on workers’ personal computers without reimbursing business expenses.
The Cox complaint’s allegations about monitoring software foreshadowed the White and Beltran complaint’s more detailed surveillance allegations — suggesting that Mercor’s use of Insightful was already generating legal scrutiny before the breach.
What Compliance Professionals Should Take Away
1. The Absence of Basic Controls Is the Plaintiff’s Best Weapon
The Gill complaint reads like a security audit finding translated into a legal brief. No MFA. No encryption at rest or in transit. No access controls. No anomaly detection. No credential rotation. For a company processing biometric data, video interviews, and identity documents, these are damning allegations.
If your organization handles similarly sensitive data, pressure-test whether these controls actually exist in practice — not just in policy documents. The gap between documented controls and operational reality is exactly where compliance theater thrives.
2. Contractor Trust Creates Legal Liability
The Esson complaint illustrates a principle that many organizations underestimate: when contractors repeatedly hand over personal information in reliance on your platform’s implied security assurances, that reliance creates a duty of care. Esson submitted a W-9 with every new engagement for twelve months. That’s not a one-time disclosure — it’s an ongoing relationship of trust that makes the breach harm concrete and documentable.
If your organization collects PII from contractors through repeated interactions, you are accumulating a legal exposure that compounds with each transaction.
3. Supply Chain Liability Is Expanding
The White and Beltran complaint doesn’t just target the company that was breached. It names the open-source library that was compromised (BerriAI/LiteLLM), the compliance vendor that certified that library’s security posture (Delve), and the unnamed companies that allegedly received surveillance-harvested data. Whether courts accept this expansive theory of supply chain liability remains to be seen, but the theory itself is a signal.
Compliance programs that evaluate only direct vendors — without assessing nth-party dependencies, the provenance of compliance certifications, and the data practices of upstream tooling — are not equipped for this threat environment. The GRC automation market needs to grapple with the Delve scandal’s implications for how certifications are generated, validated, and relied upon.
4. Surveillance Tools Create Bidirectional Risk
The White and Beltran allegations about Insightful screen captures are a warning for any organization using employee or contractor monitoring software. If your monitoring tool captures whatever is on a screen at the moment of capture — not just the specific work being performed — you may be inadvertently ingesting proprietary data belonging to third parties who never consented to monitoring.
That creates liability in two directions: toward the contractors whose personal information was captured beyond the scope of their engagement, and toward the third parties whose trade secrets, privileged communications, or confidential data appeared on contractors’ screens at the moment of capture.
5. Your Vendor’s Compliance Certification May Be Worthless
LiteLLM displayed Delve-obtained SOC 2 and ISO 27001 certifications on its website and marketing materials. Downstream users — including Mercor — relied on those certifications when making integration decisions. The White and Beltran complaint alleges those certifications were based on fabricated evidence and sham audits.
The lesson: request the actual audit report, not just the trust page badge. Verify the auditor’s AICPA accreditation independently. Ask when the audit was conducted, what the observation period was, and what controls were tested. If the vendor obtained SOC 2, ISO 27001, and HIPAA certifications bundled together for under $15,000 in under 60 days, apply serious scrutiny. Compliance at that speed and price point may be incompatible with genuine assessment.
What Happens Next
The five complaints filed so far are likely the beginning, not the end. The MercorClaims.com site suggests a larger plaintiff’s effort is being organized. Multiple law firms — including Schubert Jonckheer & Kolbe LLP and Edlesberg Law — are publicly investigating the breach. The proposed classes span over 40,000 affected individuals, and the data sensitivity (biometric information, identity documents, SSNs) exceeds what most data breach settlements have historically addressed.
The cases will likely face consolidation motions in the coming months. The three N.D. Cal. cases (Deboni, Gill, Esson) are natural candidates for consolidation or coordination, while the White and Beltran Texas case — with its broader defendant pool and more aggressive legal theories — may proceed on a separate track or face transfer motions.
Mercor’s response so far has been minimal: the company confirmed the breach, stated it was investigating with third-party forensics support, and declined to comment on the lawsuits. TechCrunch confirmed that Mercor itself was not a Delve customer — the Delve connection runs through LiteLLM, not Mercor directly. Whether that distinction matters legally is precisely what the White and Beltran complaint will test.
For the AI industry, the Mercor litigation is a preview of the regulatory and legal reckoning that was always coming. When you build a trillion-dollar industry on a foundation of open-source dependencies, third-party data vendors, gig-economy contractors, and automated compliance certifications, the first major breach doesn’t just expose data. It exposes the structural assumptions the entire ecosystem was built on.
This article is based on publicly available court dockets, media reporting from TechCrunch, Business Insider, SecurityWeek, Fortune, The Register, and Cybernews, as well as public statements from the parties involved. The allegations in the class action complaints are unproven and represent the plaintiffs’ claims. None of the defendants have been found liable for any of the allegations described. This article is provided for informational purposes only and does not constitute legal advice.