1.0 Introduction: The DoD Cybersecurity Compliance Mandate
The Department of Defense (DoD) has formalized cybersecurity accountability for its supply chain through the Defense Federal Acquisition Regulation Supplement (DFARS) and the Cybersecurity Maturity Model Certification (CMMC) program. This regulatory framework establishes that robust cybersecurity is no longer a best practice but a mandatory condition for contract awards. Defense contractors who process, store, or transmit sensitive government information are now required to demonstrate compliance through a structured, verifiable assessment process.
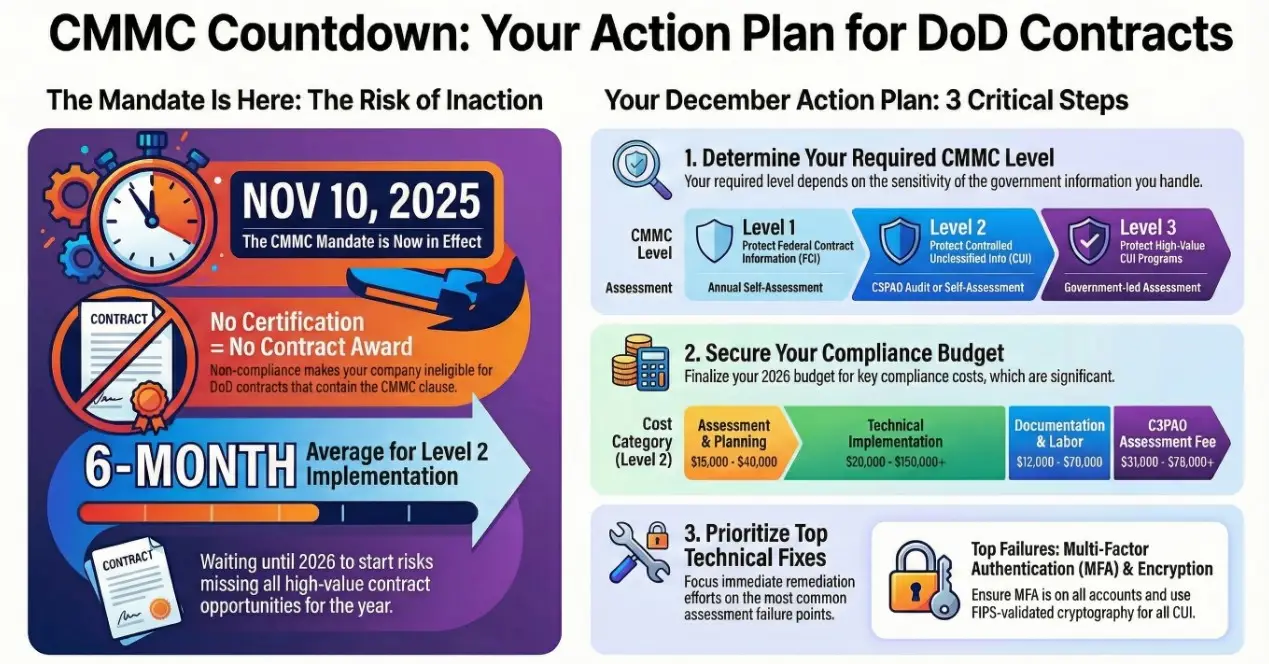
The CMMC Final Rule takes effect on November 10, 2025. This date represents a critical threshold, marking the point when the CMMC clause at DFARS 252.204-7021 will begin to appear in new DoD solicitations. This shift makes adherence to specified cybersecurity standards a direct and immediate factor in contract eligibility, rendering non-compliant organizations unable to secure new defense contracts issued after this date.
The purpose of this document is to serve as a formal guide for internal review and strategic planning. It details the procedural requirements for submitting and maintaining cybersecurity assessments in the Supplier Performance Risk System (SPRS), which the DoD has designated as its single, authorized application for this compliance data. To effectively navigate these procedures, it is essential to first understand the structure of the CMMC framework itself.
2.0 The CMMC 2.0 Framework and Required Tiers of Compliance
The CMMC 2.0 framework is a tiered model designed to assess a contractor’s cybersecurity maturity based on the sensitivity of the information they handle: Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). The program does not create new security standards for protecting CUI; rather, it provides a formal assessment and verification mechanism for the existing 110 security controls detailed in NIST SP 800-171 Rev. 2. A contractor’s required CMMC level is specified in the solicitation and dictates the scope of requirements and the type of assessment needed to prove compliance.
CMMC 2.0 Compliance Levels
Level
Information Protected & NIST Alignment
Assessment & Affirmation Requirements
Level 1
Federal Contract Information (FCI)
Aligns with the 15 basic safeguarding requirements from FAR 52.204-21.
Annual Self-Assessment and affirmation of compliance in SPRS. No Plan of Actions and Milestones (POA&Ms) are permitted; full compliance is required.
Level 2
Controlled Unclassified Information (CUI)
Aligns with all 110 security requirements from NIST SP 800-171 Rev. 2.
Triennial Assessment (every 3 years). The assessment type is contract-specific and will be either a Self-Assessment or a formal C3PAO Assessment. POA&Ms are allowed for certain controls but must be closed within 180 days.
Level 3
CUI for High-Value Programs
Aligns with all 110 requirements of NIST SP 800-171 plus 24 enhanced requirements from NIST SP 800-172.
Triennial Government-Led Certification Assessment conducted by the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC).
The DoD is implementing CMMC requirements through a phased, multi-year timeline, giving contracting officers discretion in applying the clauses to new solicitations. Phase 1 begins on November 10, 2025, and Phase 4, which marks full implementation, begins on November 10, 2028. This phased approach allows the industry time to prepare but underscores the urgency for organizations to understand the distinct pathways for achieving and reporting their compliance status.
CMMC & NIST 800-171 Compliance Assessment Tool
3.0 Assessment Pathways and Foundational Requirements
Before any submission to SPRS can occur, an organization must undergo a specific type of assessment as dictated by its contractual obligations. While the DoD previously required contractors handling CUI to conduct a NIST SP 800-171 self-assessment, the CMMC program formalizes this process with distinct verification pathways tied to the sensitivity of the information involved.
The following assessment types are available to contractors:
- NIST SP 800-171 Basic Assessment: This is the foundational self-assessment required under DFARS 252.204-7019/7020. Contractors must conduct a self-evaluation against the NIST SP 800-171 controls, calculate a score based on the DoD Assessment Methodology, and post that score to SPRS.- CMMC Level 1 Self-Assessment: This is an annual requirement for organizations that handle only FCI. The organization must conduct a self-assessment and affirm that all 15 basic safeguarding requirements from FAR 52.204-21 are met.- CMMC Level 2 Self-Assessment: For certain contracts involving non-critical CUI, contractors may be permitted to conduct a triennial self-assessment. This requires a comprehensive self-evaluation against all 110 controls in NIST SP 800-171.- CMMC Level 2 Certification Assessment: Required for contracts involving more sensitive CUI, this is a formal audit conducted by an accredited CMMC Third-Party Assessment Organization (C3PAO). The C3PAO verifies the contractor’s implementation of the 110 NIST SP 800-171 controls.- CMMC Level 3 Certification Assessment: This is the highest level of assessment, reserved for contractors supporting the most sensitive DoD programs. It is a government-led assessment conducted by the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC).
Regardless of the assessment type performed, the results must be formally entered, affirmed, and maintained within the Supplier Performance Risk System to ensure contract eligibility.
4.0 Procedural Guide for SPRS Submissions and Affirmations
The Supplier Performance Risk System (SPRS) is the DoD’s central repository for all contractor cybersecurity compliance data. Proper registration and the accurate, timely entry of assessment results are critical prerequisites for contract eligibility. This section provides the step-by-step procedures for fulfilling these requirements, based directly on the official SPRS Software User’s Guide.
4.1 Accessing SPRS and User Role Requirements
To gain access to SPRS, users must first have an active account with the Procurement Integrated Enterprise Environment (PIEE). Additionally, their company must be registered in the System for Award Management (SAM). Once these prerequisites are met, users can request specific roles within SPRS.
There are two key vendor roles relevant to cybersecurity assessment submissions:
- Contractor/Vendor (Support Role): This role provides view-only access to company reports, including Cyber Reports (NIST and CMMC). It is suitable for personnel who need to review compliance status but are not responsible for data entry.- SPRS Cyber Vendor User: This is a privileged role required for submitting assessment results. It grants the user the ability to add, edit, and affirm NIST and CMMC assessments for the authorized CAGE code and its associated hierarchy.
4.2 Submitting a NIST SP 800-171 Basic Assessment
The following steps, derived from the SPRS Software User’s Guide, outline the procedure for submitting a NIST SP 800-171 Basic Self-Assessment in SPRS, as required under DFARS 252.204-7019/7020.
- Navigate to the Cyber Reports (CMMC & NIST) module from the main menu.2. Select the NIST SP 800-171 Assessments tab. This will display existing assessments.3. Click the Add New NIST Assessment button to open the data entry screen.4. Enter all required information into the assessment details form. Key data fields include:
- Assessment Date: The date the self-assessment was completed.- Assessment Score: The calculated score based on the DoD Assessment Methodology.- Assessing Scope: Select Enterprise, Enclave, or Contract.- Plan of Action Completion Date: The estimated date that all remaining deficiencies will be resolved. This is required for any score less than 110.- System Security Plan (SSP) Assessed: The document name of the SSP that was reviewed.- SSP Date: The date of the SSP document.- Included CAGE(s): A comma-delimited list of all CAGE codes covered by the assessment.5. Click the Save button to submit the assessment.
Once saved, the assessment is assigned a DoD Unique Identifier (UID) and becomes visible to authorized government personnel. Any assessment with an Assessment Date older than three years will be highlighted in red, indicating that it has expired and is no longer current.
4.3 Submitting and Affirming a CMMC Level 1 Self-Assessment
The following steps, derived from the SPRS Software User’s Guide, outline the procedure for entering a CMMC Level 1 Self-Assessment, which involves both data entry and a formal affirmation by a senior company official.
- Navigate to the Cyber Reports (CMMC & NIST) module and select the CMMC Assessments tab.2. On the CMMC Level 1 (Self) subtab, click the Add New CMMC Level 1 Self-Assessment button.3. Enter the required assessment details, including:
- Assessment Date- Assessment Scope (Enterprise or Enclave)- Company Size (total number of employees)- Compliance status for FAR clause 52.204-21 (Yes or No)- **Included CAGE(s)**4. Once all details are entered, click Continue to Affirmation to begin the affirmation process.
The Affirmation Process is a critical final step. The individual responsible for this action is the Affirming Official (AO), defined as a senior-level representative with the authority to ensure the organization’s compliance. There are two pathways for completing the affirmation:
- If the user entering the data is the designated AO, they can proceed directly by clicking Continue to Affirmation, reviewing the certification statement, and clicking Affirm.2. If the user is not the AO, they must enter the AO’s email address and click Transfer to AO. This action sends an email notification to the AO and places the assessment in a “Pending Affirmation” status until the AO logs in and completes the process.
A CMMC Level 1 self-assessment is valid for one year. After this period, its status in SPRS will automatically change to “No CMMC Status (Expired Assessment).“
4.4 Submitting and Affirming a CMMC Level 2 Self-Assessment
The following steps, derived from the SPRS Software User’s Guide, outline the procedure for completing a CMMC Level 2 Self-Assessment, which is a more detailed process requiring attestation for each of the 110 security controls.
- Navigate to the CMMC Assessments tab and select the CMMC Level 2 (Self) subtab.2. Click the Add New CMMC Level 2 Self-Assessment button.3. A stepper tool will guide you through each of the 14 requirement families (e.g., Access Control, Incident Response). For each of the 110 controls listed, you must select a compliance status of “Met,” “Not Met,” or “N/A.”4. After completing all requirements, proceed to the Review step to verify your entries.5. In the CAGEs step, define the Assessment Scope, Company Size, and list all Included CAGE(s).6. Click Save and Continue to proceed to the Score step, where SPRS will display the final calculated score and the resulting CMMC status type.7. Based on the score, the potential outcomes are “No CMMC Status,” “Unaffirmed CMMC L2 Conditional Self-Assessment,” or “Unaffirmed CMMC L2 Final Self-Assessment.” Only assessments with a Conditional or Final status can be affirmed.8. If the assessment is eligible for affirmation, follow the same two-pathway affirmation process involving the Affirming Official (AO) as described for the Level 1 assessment.
4.5 Affirming C3PAO and DIBCAC Assessments
For CMMC Level 2 assessments conducted by a C3PAO and Level 3 assessments led by DIBCAC, the assessing organization is responsible for entering the assessment data into the DoD’s systems. However, the contractor is still required to perform an initial affirmation and subsequent annual affirmations in SPRS to keep the certification active.
The vendor’s affirmation responsibilities for these third-party assessments include:
- Locating the assessment record in the appropriate subtab within SPRS (e.g., “CMMC Level 2 (C3PAO)” or “CMMC Level 3 (DIBCAC)”).- Initiating the affirmation process by clicking the Affirm button.- Reviewing all assessment details entered by the assessor to ensure their accuracy.- During annual affirmations, updating the Company Size and removing any CAGEs that are no longer in the assessment scope.- Ensuring the designated Affirming Official (AO) completes the process by certifying and submitting the affirmation.
Successfully affirming these assessments is essential for activating and maintaining the official certification status in SPRS.
5.0 Maintaining Compliance and Managing Subcontractor Risk
Achieving a CMMC certification or posting a NIST SP 800-171 assessment is a critical milestone, but maintaining compliance is a continuous operational requirement. Failure to maintain an active and current status in SPRS can result in immediate ineligibility for new contract awards or the exercise of contract option years.
CMMC Level 2 and Level 3 certifications are valid for three years, but they require an annual affirmation in SPRS to remain current. An “Affirm” button will become available in the system 60 days prior to the affirmation expiration date. If an organization fails to complete this annual affirmation by the deadline, its certification status will change to “(Expired Affirmation),” jeopardizing its standing as a compliant contractor.
Subcontractor Compliance Verification
A critical and often overlooked aspect of ongoing compliance is the subcontractor flow-down requirement stipulated in DFARS 252.204-7020. A prime contractor is legally responsible for ensuring that all of its tiered subcontractors have a current, passing assessment result recorded in SPRS before awarding any subcontract or purchase order that involves CUI.
This procedural requirement creates a significant operational risk: if a critical-path subcontractor is found to be non-compliant in SPRS during a pre-award check, the prime contractor is legally barred from flowing down the work. This can halt project timelines, force costly re-sourcing efforts, and jeopardize the prime’s ability to execute its contractual obligations. Therefore, primes must integrate a formal SPRS verification step into their procurement and supply chain management processes.
6.0 Conclusion and Strategic Recommendations
Adherence to the detailed submission and affirmation procedures within the Supplier Performance Risk System is not merely an administrative task; it is a direct factor in contract eligibility and a key element of the DoD’s broader cybersecurity strategy. As CMMC requirements become standard in DoD solicitations, maintaining a current and accurate compliance posture in SPRS is foundational to remaining a viable partner in the Defense Industrial Base.
Key Strategic Actions for Internal Planning
- Assign Administrative Oversight: Designate a specific role, such as the Affirming Official (AO), with clear responsibility for managing the organization’s SPRS account. This includes overseeing all initial submissions and ensuring the annual affirmation cadence is met to prevent administrative lapses.2. Establish a Formal Submission Process: Document the internal procedures for gathering the required data for each assessment type—including SSP name, dates, assessment scope, CAGEs, and scores—to ensure accuracy and consistency before any information is entered into SPRS.3. Integrate Subcontractor SPRS Verification: Implement a mandatory pre-award checkpoint in the procurement process to verify and document the current SPRS compliance status of all potential subcontractors. This mitigates supply chain risk and ensures adherence to DFARS flow-down requirements.4. Maintain Documentation Alignment: Ensure the System Security Plan (SSP) and any associated Plan of Action & Milestones (POA&M) are kept current and precisely match the information submitted to SPRS. This alignment is critical for withstanding the scrutiny of C3PAO or government-led assessments.