How a machine-readable lifecycle standard will finally solve the EOL tracking chaos—and why you need to prepare now
The $4.4 Million Question Nobody Can Answer
Here’s a question that should terrify every compliance officer: Can your organization produce, within 24 hours, a complete inventory of every software component and hardware device that has reached end-of-life status?
For most organizations, the answer is an uncomfortable silence followed by vague references to “the spreadsheet IT maintains” or “we think procurement tracks that.”
This blind spot is no longer theoretical. Edge device exploitation—targeting VPNs, firewalls, and routers—jumped from 3% of all breaches in 2024 to a staggering 22% in 2025, according to the Verizon Data Breach Investigations Report. Nation-state actors have systematically weaponized unsupported network infrastructure, exploiting devices that can never be patched because vendors stopped providing security updates.
The average cost of a supply chain security incident: $4.4 million. The root cause in a growing number of cases: organizations running end-of-life software they didn’t even know was unsupported.
CISA and an international coalition of technology vendors have decided enough is enough. Enter OpenEoX—a new OASIS OPEN international standard that promises to make end-of-life tracking as automated and reliable as vulnerability scanning. If you work in compliance, security, or IT procurement, this standard is about to fundamentally change your operational workflows.
Here’s everything you need to know to prepare.
Ransomware Attacks Soar 30% in 2026: Inside the Unprecedented Surge
What Is OpenEoX? The Technical Foundation
OpenEoX is a machine-readable standard for communicating software and hardware lifecycle information. Co-chaired by CISA and Cisco through the OASIS Technical Committee, it defines a JSON-based schema that standardizes how vendors communicate four critical lifecycle milestones:
MilestoneWhat It Means for You**General Availability (GA)The first ship date—when support obligations beginEnd of Sales (EoS)Last day to purchase from vendor channelsEnd of Security Support (EoSSec)The critical date: no more security patchesEnd of Life (EoL)**All vendor support terminates
The critical distinction here is End of Security Support—the date after which security vulnerabilities will never be patched. This is the date compliance teams actually care about, and it’s often buried deep in vendor documentation or never explicitly stated at all.
Why Machine-Readable Matters
Today, lifecycle information exists in a chaotic mix of formats: PDF announcements buried in vendor support portals, blog posts, marketing pages, or sometimes just customer service representatives who “think” support ended last year. The OpenEoX standard changes this by providing:
- Standardized JSON format that tools can automatically consume- Consistent terminology across all vendors and platforms- Direct integration with SBOMs, vulnerability scanners, and compliance tools- Vendor-authoritative data published directly by the source
Think of it as DNS for product lifecycles. Instead of manually searching for every vendor’s support policy, your security tools will query standardized feeds and automatically flag approaching EOL dates.
Why This Is Urgent: The Edge Device Crisis
The timing of OpenEoX isn’t coincidental. We’re in the middle of an edge device exploitation epidemic that has fundamentally shifted the threat landscape.
The Numbers Are Alarming
The statistics from 2025 paint a clear picture:
- Edge device breaches: 3% of all breaches (2024) → 22% of all breaches (2025)- Zero-days targeting edge devices: 22 operating system-level vulnerabilities in 2024, up from 17 in 2023- Same-day exploitation: 28.96% of Known Exploited Vulnerabilities (KEVs) were exploited within 24 hours of disclosure in 2025- Initial access via exploitation: 21% of ransomware attacks used vulnerability exploitation as the entry point (Mandiant M-Trends 2025)
What’s Driving the Surge?
Nation-state actors have discovered that edge devices represent the perfect target:
- Always internet-facing by design2. Rarely updated compared to endpoint systems3. Invisible to EDR and most security tooling4. Persistent access once compromised—firmware implants survive reboots5. Legacy devices forgotten in network closets, running unsupported code
The UNC5221 campaign (attributed to China-nexus actors) has repeatedly targeted Ivanti products, exploiting CVE-2023-46805, CVE-2024-21887, and CVE-2025-22457 in succession. Fortinet devices have been systematically compromised through multiple vulnerabilities. D-Link routers running discontinued firmware have been targeted with zero-days that will never receive patches.
The “Abandonware” Problem
Research by Sergii Demianchuk, an OpenEoX Technical Committee member, reveals an even more insidious problem: 42% of actively used open-source software shows signs of decline—reduced commit frequency, slowing issue closure, infrequent releases.
Many projects effectively die before any formal EOL announcement. Organizations continue running this “abandonware” without realizing they’re operating unsupported software with accumulating, unfixable vulnerabilities.
OpenEoX aims to surface this information automatically, enabling organizations to identify at-risk components before they become incident headlines.
CISA Is Secretly Updating Its Vulnerability Catalog—And Your Security Team Is Probably Missing It
The Compliance Mandate Is Already Here
If you’re waiting for a compliance framework to require EOL tracking before taking action, you’re already behind. The requirements exist today.
PCI DSS 4.0 Requirements (Mandatory Since March 2025)
PCI DSS 4.0 Control 12.3.4 requires organizations to maintain a comprehensive technology asset inventory that includes lifecycle status. Specifically, the standard mandates:
- Identification of technologies no longer receiving security updates- Risk assessment for end-of-life components- Documentation of compensating controls or remediation plans- Regular review of technology lifecycle status
For organizations handling payment card data, the inability to demonstrate EOL awareness during an audit is now a finding—not just a recommendation.
CISA Binding Operational Directive 26-02
Issued in February 2026, BOD 26-02 directly addresses the edge device crisis:
- May 5, 2026: Federal agencies must report complete inventory of end-of-support edge devices and remediation plans to CISA- February 2027: All end-of-support edge devices must be removed from federal networks
While BOD directives only legally bind federal agencies, they establish the standard of care for the entire industry. Private sector organizations face increasing pressure to meet similar benchmarks, particularly those working with government contracts or operating in regulated industries.
NIST SSDF and Software Supply Chain Requirements
NIST’s Secure Software Development Framework (SSDF) practices PW.4.1 and PW.4.4 require organizations to verify the sustainability and support status of software dependencies. Executive Order 14028 formalized these requirements for federal software suppliers.
If you’re a vendor selling to the federal government, demonstrating lifecycle awareness for your components isn’t optional—it’s a procurement requirement.
CISA Under Siege: Trump’s Nominee Promises Funding Amid Agency Overhaul
Who’s Adopting OpenEoX?
The coalition behind OpenEoX represents a who’s-who of enterprise technology:
Founding Vendors and Contributors
OrganizationRoleWhy It MattersCiscoCo-Chair (Omar Santos)Network infrastructure giant; originated OpenEoX conceptMicrosoftContributorCovers Windows, Azure, Office ecosystem lifecycle dataRed HatContributorEnterprise Linux and OpenShift lifecycle visibilityHuaweiContributorGlobal telecom and network equipmentIBMParticipantEnterprise software and mainframe systemsDellParticipantHardware lifecycle for servers, storage, endpointsOracleParticipantDatabase and enterprise application lifecycles
Government Backing
AgencyRoleCISA (US)Co-Chair; driving federal adoptionBSI (Germany)Federal Office for Information Security; TC memberNSACollaboration partner on framework development
This level of government and industry alignment is rare. When CISA co-chairs a standard alongside major vendors, that standard typically becomes mandatory within 2-3 years.
Integration: How OpenEoX Fits Your Existing Tools
OpenEoX doesn’t replace your vulnerability management infrastructure—it completes it. The standard is designed to integrate seamlessly with the security data ecosystem you’re already building:
Asset Inventory → SBOM → CSAF/VEX → OpenEoX
("what we run") ("what it ("what's ("is it still
contains") vulnerable") supported?")
With SBOM (Software Bill of Materials)
OpenEoX data can be embedded or referenced in SBOMs, enabling lifecycle-aware dependency tracking. When your next SBOM scan runs, it could automatically flag that three of your dependencies are approaching end-of-security-support.
With CSAF/VEX (Vulnerability Exchange)
VEX tells you whether a vulnerability affects your environment and whether a fix exists. OpenEoX adds the critical context: will a fix ever exist? A high-severity CVE affecting an EOL component requires a fundamentally different response than the same CVE on supported software.
Practical Workflow Impact
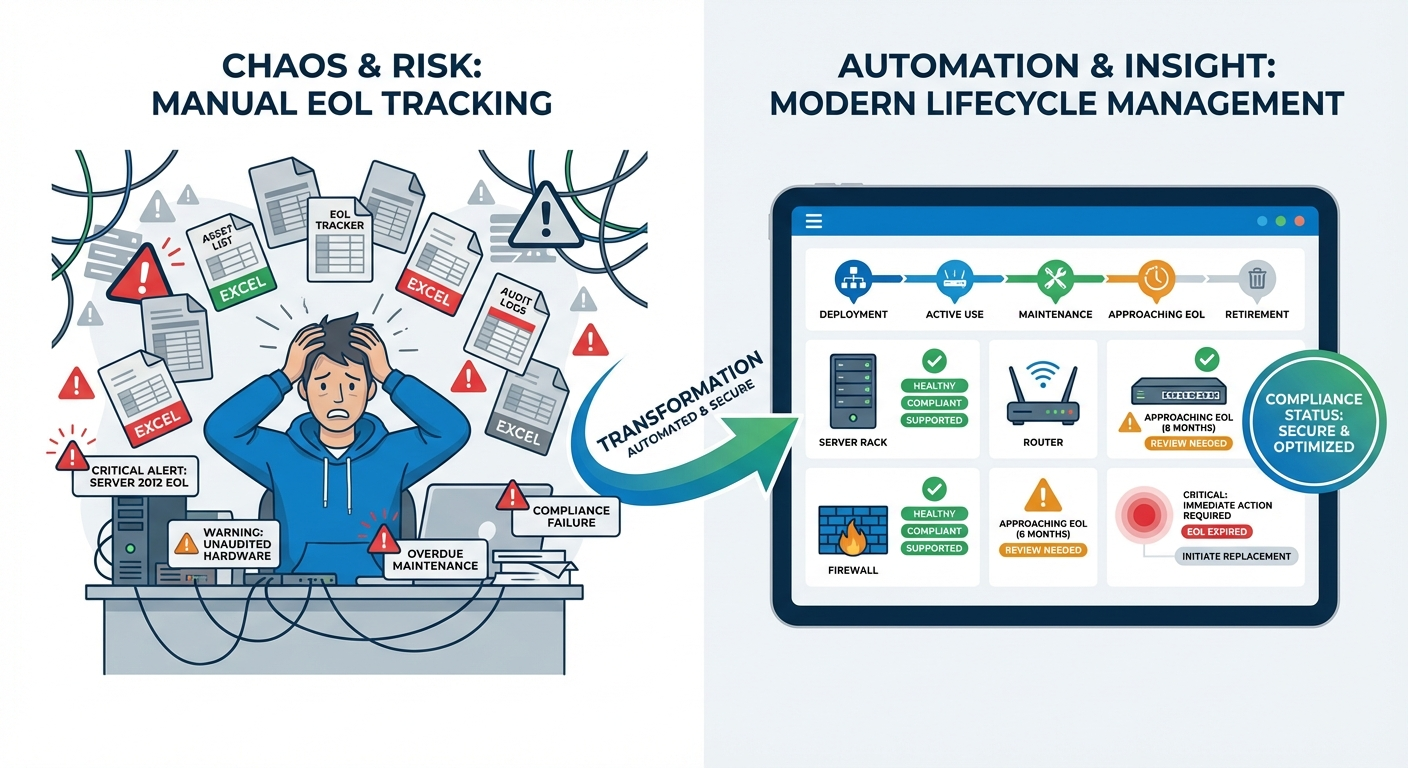
Before OpenEoX (Current State):
- Discover vulnerability in component2. Search vendor website (manually)3. Find buried EOL notice (maybe)4. Update spreadsheet (hope someone does)5. Hope someone checks before renewal
After OpenEoX (Future State):
- Automated scan pulls OpenEoX feeds2. EOL approaching dates flagged 6-12 months in advance3. Risk scoring automatically weights supportability4. Tickets auto-generated for refresh planning5. Procurement alerted during budget cycles
The shift from reactive to proactive lifecycle management represents the core operational benefit.
How to Prepare: A Practical Implementation Roadmap
OpenEoX is in active development, with the technical committee refining specifications through 2026. The full OASIS standard ratification is expected by late 2026 or early 2027. Here’s how compliance-focused organizations should prepare:
Phase 1: Assess Current State (Q1-Q2 2026)
Inventory your lifecycle tracking:
- How do you currently track EOL/EOS dates?- Who owns the process? (IT? Security? Procurement? Nobody?)- How many hours per month does manual tracking consume?- When did you last audit edge device support status?
Quantify the gap:
- List all vendors whose lifecycle data you need- Identify how each currently communicates EOL information- Document integration points with existing tools (SIEM, ticketing, CMDB)
Benchmark metrics:
- Average time from EOL announcement to organizational awareness- Percentage of assets with documented lifecycle dates- Number of EOL exceptions currently in production
Phase 2: Establish Foundation (Q2-Q3 2026)
Standardize internal terminology:
- Adopt the OpenEoX four-milestone model (GA, EoS, EoSSec, EoL)- Update asset management schemas to include lifecycle fields- Train procurement and IT on consistent definitions
Evaluate tooling readiness:
- Contact your SBOM, vulnerability scanner, and CMDB vendors- Ask: “What’s your OpenEoX integration roadmap?”- Prioritize vendors with clear adoption plans
Update procurement language:
- Require vendors to provide lifecycle information in contracts- Ask: “Will you publish OpenEoX-compliant lifecycle data?”- Include lifecycle transparency as a vendor selection criterion
Phase 3: Pilot Integration (Q4 2026)
Start with high-risk asset classes:
- Edge devices (VPNs, firewalls, routers)—the current threat focus- End-user operating systems- Critical business applications
Build automated workflows:
- Connect lifecycle feeds to ticketing systems- Create escalation triggers for approaching EOL dates- Establish governance for EOL exception requests
Document compliance evidence:
- Prepare audit artifacts demonstrating proactive monitoring- Create reports showing lifecycle coverage percentages- Build dashboards for executive visibility
Phase 4: Scale and Optimize (2027+)
Expand coverage:
- Roll out to all asset classes- Include open-source dependencies via SBOM integration- Automate vendor onboarding processes
Measure improvement:
- Reduction in manual tracking hours- Time-to-awareness for new EOL announcements- Audit finding reduction in lifecycle-related controls
ROI: Making the Business Case
For budget-conscious organizations, OpenEoX adoption provides measurable returns:
Investment AreaProjected BenefitManual tracking elimination40-60 hours/month recovered (enterprise avg.)Supply chain incident prevention$4.4M average incident cost avoidedAudit preparationAutomated evidence generationProcurement efficiencyPre-planned refresh cycles, better negotiationRisk reductionProactive decommissioning before exploitation
The organizations that prepare now will establish competitive advantages: faster audit cycles, reduced breach risk, and smoother procurement processes.
What’s Next: Key Dates to Track
DateMilestoneNowOpenEoX Technical Committee actively developing specificationMay 5, 2026Federal agencies report EOS device inventory to CISAQ3-Q4 2026Expected: Major vendor pilot OpenEoX feedsFebruary 2027Federal agencies must remove EOS edge devices2027Expected: Full OASIS OpenEoX Standard ratification
The Bottom Line
The era of treating EOL tracking as a manual, ad-hoc process is ending. OpenEoX represents the standardization that compliance professionals have needed for years—machine-readable, vendor-authoritative lifecycle data that integrates with the security tools you already use.
The organizations that prepare now—assessing current gaps, establishing internal standards, and engaging vendors on integration plans—will be positioned to adopt OpenEoX smoothly when it reaches maturity. Those that wait will face another scramble to meet compliance requirements with inadequate tooling.
As Sergii Demianchuk, OpenEoX Technical Committee member, observed: “Adoption of OpenEoX could become as fundamental to cybersecurity assurance as CVE is to vulnerability management.”
Given the edge device crisis driving current breach statistics, that future can’t arrive soon enough.
Key Takeaways
- OpenEoX is a machine-readable standard for EOL/EOS tracking, co-chaired by CISA and Cisco2. Edge device breaches jumped from 3% to 22% of all incidents—unsupported devices are a primary target3. PCI DSS 4.0 already requires EOL tracking; CISA BOD 26-02 mandates federal compliance by 20274. Major vendors are onboard: Microsoft, Cisco, Red Hat, IBM, Dell, Oracle, and government agencies5. Start preparing now: Assess current gaps, standardize terminology, engage vendors on integration
For compliance frameworks, implementation guides, and regulatory updates, subscribe to ComplianceHub Weekly.