1.0 The Strategic Imperative: Beyond Compliance to Enhanced Resilience
The Digital Operational Resilience Act (DORA) is not merely another regulation; it represents a non-negotiable shift in our operating environment. This fundamental change will separate market leaders who leverage resilience for competitive advantage from laggards who treat it as a compliance burden. We will treat DORA as a strategic catalyst for enhancing our operational stability and market standing. This document presents our definitive plan to transform this regulatory mandate into a long-term business advantage.
The evolution from a narrow cybersecurity focus to a comprehensive resilience strategy is at the heart of DORA. Historically, our efforts centered on securing ICT systems against specific threats. While essential, this approach is no longer sufficient. In today’s deeply interconnected financial system, a minor ICT disruption can cascade into a systemic event. DORA mandates a shift towards a holistic strategy that ensures we can anticipate, withstand, recover from, and adapt to any and all ICT-related disruptions, thereby safeguarding not only our institution but also contributing to the stability of the entire financial market.
Embracing DORA’s requirements presents several significant business opportunities that align directly with our strategic goals:
- Enhanced Customer Trust: By adhering to DORA’s stringent resilience standards, we demonstrate an unwavering commitment to safeguarding client assets and ensuring service availability. This builds stronger, more loyal customer relationships and enhances our reputation as a stable and reliable partner.- Significant Competitive Advantages: Proactively adopting DORA’s advanced standards positions us as a market leader. This becomes a key market differentiator that attracts risk-averse clients who prioritize security and reliability, driving business growth.- Superior Recoverability: DORA mandates a rigorous approach to business continuity and recovery. This ensures that in the event of an incident, we can swiftly restore critical functions, minimize downtime, and protect data integrity, transforming resilience from a defensive necessity into a strategic advantage.
DORA’s principles-based approach empowers us to tailor our resilience framework to our unique operational context and risk profile. This flexibility is a call to move beyond a “checking-the-boxes” compliance mindset. By integrating digital resilience into our core business strategy, we will foster a culture of continuous improvement and meaningful risk management. This proactive stance ensures that resilience is not an isolated function but an integral part of every strategic decision we make.
2.0 The DORA Regulatory Framework: Core Pillars and Obligations
A clear understanding of the Digital Operational Resilience Act’s core components is essential for effective strategic planning and execution. DORA is not a monolithic set of rules; it is a structured framework built upon foundational pillars, each with specific obligations. This section deconstructs the regulation to provide the executive team with a clear overview of our key responsibilities.
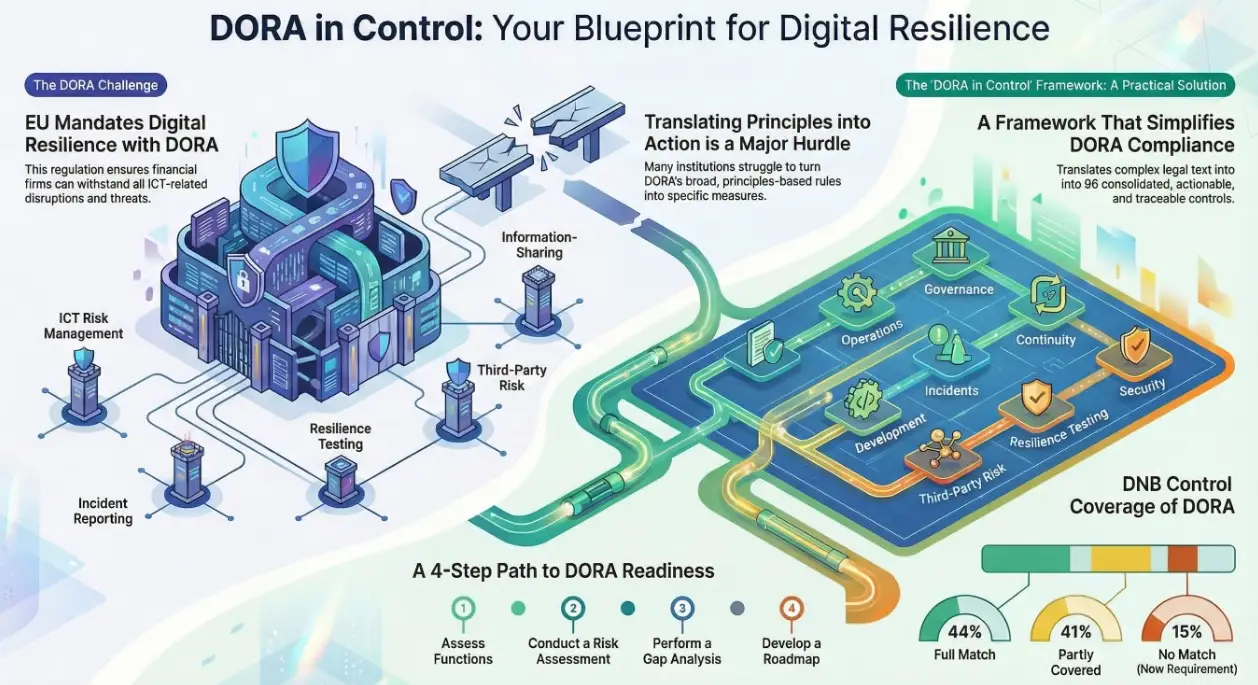
DORA’s requirements are organized around five foundational pillars that form a comprehensive structure for achieving digital operational resilience:
- ICT risk management: This pillar requires the establishment of a comprehensive framework to effectively identify, protect against, detect, respond to, and recover from all types of ICT-related risks, emphasizing strong governance and continuous improvement.2. Incident management, classification, and reporting: This pillar mandates a standardized process for managing, classifying, and reporting significant ICT-related incidents to the relevant authorities, harmonizing reporting and enhancing collective resilience.3. Digital operational resilience testing: This pillar mandates a rigorous, continuous testing program to validate our defenses. This includes both routine assessments and, for designated entities, advanced threat-led penetration testing (TLPT) that simulates sophisticated, real-world cyberattacks.4. Managing of ICT third-party risks: Recognizing the sector’s reliance on external providers, this pillar requires thorough due diligence, stringent contractual agreements, and continuous monitoring of all third-party providers, especially those supporting critical functions.5. Information-sharing arrangements: This pillar promotes the voluntary exchange of cyber threat intelligence and best practices among financial entities to foster a collaborative defense network and improve the overall resilience of the financial sector.
The DORA regulation follows a two-level structure. The primary legislation, or “level 1,” is the act itself, which outlines the core principles and high-level requirements across its 64 articles. This is supplemented by secondary legislation, or “level 2,” which consists of Regulatory Technical Standards (RTS) and Implementation Technical Standards (ITS). These technical standards are drafted by the European Supervisory Authorities (ESAs) to specify the precise technical requirements needed to comply with the level 1 text.
This complex, multi-layered regulatory structure demands more than a reactive checklist; it requires a unified, strategic framework to ensure coherent and efficient implementation.
3.0 Our Strategic Solution: The NOREA DORA in Control Framework
While DORA’s principles-based nature offers valuable flexibility, it also presents significant implementation challenges. Translating broad principles into specific, actionable measures requires a unified interpretation across legal, IT, and business domains. To overcome these hurdles and ensure a consistent, efficient path to compliance, we have adopted the NOREA “DORA in control framework” as our strategic implementation tool.
The primary purpose of the DORA in control framework is to transform the legal and technical complexities of the regulation into a clear, understandable, and actionable set of strategies and controls. It is designed to bridge the gap between DORA’s high-level principles and the practical measures required for implementation, providing a structured approach that simplifies compliance and enhances our overall digital resilience.
The framework provides several key features that offer distinct strategic advantages for our implementation project:
Framework Feature
Strategic Advantage
Simplified Legal Interpretation
Translates complex legal text from DORA’s articles, RTS, and ITS into accessible language. This ensures consistent understanding across legal, IT, and business units, reducing ambiguity and implementation risk.
Consolidated Actionable Controls
Distills DORA’s requirements into a cohesive set of 95 individual controls organized across 8 recognizable domains and 28 sub-domains (e.g., Governance, Third-party Risk). This provides a clear, traceable path from regulatory articles to required actions.
Integration of DNB Maturity Model
Incorporates the maturity model from the Dutch Central Bank (DNB) Good Practice for Information Security. This allows us to systematically assess and track our progress against established benchmarks, providing a data-driven view of our compliance journey.
Visual Progress Dashboard
Includes a dashboard that provides a clear, intuitive visual representation of our implementation status. This facilitates effective communication and reporting to the Management Body, key stakeholders, and supervisory authorities.
By leveraging this comprehensive framework, we move from interpreting a complex regulation to executing a clear and manageable plan. This structured approach provides the foundation for the actionable roadmap detailed in the following section.
4.0 The Four-Phase Implementation Roadmap
Our DORA implementation will proceed as a structured, four-phase program. This official roadmap ensures a methodical and auditable path to full compliance by the 17 January 2025 deadline, leaving no room for ambiguity.
4.1 Phase 1: Foundational Assessment & Scoping
- **Key Objectives & Activities:**Identify and comprehensively document all business functions classified as “critical and/or important” to the institution’s operations.- Map and inventory all supporting ICT infrastructure, systems, and assets that underpin these critical functions.- Document all dependencies on ICT third-party providers, paying special attention to those supporting critical functions.
4.2 Phase 2: Risk Assessment & Prioritization
- **Key Objectives & Activities:**Perform a thorough risk assessment on the ICT infrastructure and third-party services identified in Phase 1.- Establish a detailed risk profile that identifies key vulnerabilities, threats, and potential impacts on our critical functions.- Prioritize areas of focus for remediation and control implementation based on the established risk profile.
4.3 Phase 3: Gap Analysis & Control Mapping
- **Key Objectives & Activities:**Deploy the NOREA DORA in control framework to conduct a comprehensive gap analysis.- Systematically compare our current state of controls and processes against the 95 specific controls required by DORA.- Identify and document all areas where our existing measures fall short of the regulation’s requirements.
4.4 Phase 4: Remediation Planning & Execution
- **Key Objectives & Activities:**Develop a formal remediation roadmap and project plan based on the findings from the gap analysis.- Define specific solutions, mitigating measures, and implementation timelines to address all identified gaps.- Execute the plan, focusing on addressing root causes to ensure sustainable compliance and enhanced resilience.
This roadmap is designed to be executed under a robust governance structure, which provides the necessary oversight and accountability to ensure its success.
5.0 Governance and Critical Success Factors
Successful DORA implementation and the cultivation of a resilient organizational culture are contingent on strong governance, clear accountability, and unwavering leadership. This section defines the roles, responsibilities, and strategic perspectives that are essential for achieving and sustaining digital operational resilience.
Management Body Accountability
The ultimate responsibility for managing all ICT risks rests with the Management Body; this responsibility cannot be delegated. The Management Body is charged with direct oversight of the DORA implementation project and must ensure that digital operational resilience is embedded within the institution’s overall business strategy. Key governance duties include:
- Establishing and approving all key policies related to ICT risk, business continuity, and third-party provider management.- Defining and enforcing clear roles and responsibilities for all ICT-related functions.- Setting and approving the institution’s digital operational resilience strategy, including risk tolerance levels.- Staying continuously informed of critical third-party arrangements and approving any material changes that could impact the institution’s risk profile.- Allocating the necessary budget and resources to fulfill our resilience objectives.- Periodically reviewing internal ICT audit plans and their findings to ensure effectiveness.
By personally overseeing these duties, the Management Body directly champions the resilience culture that underpins our competitive differentiation and enhances customer trust.
Engineering Perspective and Continuous Improvement
To achieve sustainable resilience, we must adopt an “engineering perspective”—a systematic approach focused on solving the root causes of issues rather than merely treating symptoms. This requires a culture of continuous learning and adaptation, informed by data from our risk assessments, incident reviews, resilience tests, and audits. By dissecting complexities and applying structured problem-solving, we move beyond compliance as a checklist and build a truly robust operational environment.
Third-Party Risk Management
Our increasing reliance on outsourced ICT services makes third-party risk management a critical component of our DORA strategy. It is imperative that we manage relationships with all ICT third-party providers, especially those supporting critical functions, with the same rigor we apply to our internal systems. We must ensure that all third-party contracts include provisions for resilience and security, that their performance is continuously monitored, and that their services align fully with our institutional resilience posture and regulatory obligations.
This robust governance model provides the engine for implementation; the following section details the dashboard we will use to navigate and report on our progress.
6.0 Measuring and Reporting Progress
A data-driven approach to tracking progress is crucial for demonstrating compliance to both internal stakeholders and supervisory authorities. This section outlines the mechanisms we will use to measure our maturity and report our status effectively.
Our progress will be tracked using the integrated features of the DORA in control framework. The framework’s incorporation of the DNB maturity model will allow us to systematically assess our implementation level for each of the 95 controls, providing a clear and objective measure of our progress. This data will feed directly into the framework’s visual dashboard, which will offer an intuitive, at-a-glance overview of our compliance status and serve as the primary tool for communicating progress to the Management Body.
This structured reporting capability is not just a best practice; it is a strategic necessity. Supervisory authorities have already announced that they will request organizations to submit formal gap assessments and roadmaps for compliance. The reporting mechanisms enabled by our chosen framework will ensure we can meet these requests promptly and professionally.
To further streamline our efforts, the framework helps us leverage existing work. Many of our current controls, based on the former DNB Good Practice for Information Security, can be mapped directly to DORA’s requirements. This mapping helps us efficiently transition from existing standards to the new regulation.
Leveraging Existing Frameworks: DORA vs. DNB Control Overlap
Overlap Category
Percentage of DORA Controls
Full match
44%
Partly covered
41%
No match
15%
This analysis is critical for resource allocation, highlighting that the most significant gaps lie in Continuity Management, Security Management, Third-party Risk Management, and Incident Management. Our remediation efforts must be disproportionately focused on these domains. This structured approach to measurement provides the assurance needed to move forward with confidence.
7.0 Conclusion: From a Resilient Foundation to Market Leadership
The successful execution of this strategic plan will achieve far more than simply meeting the requirements of the Digital Operational Resilience Act. By committing to this structured, four-phase journey, we are not just preparing for regulatory scrutiny; we are fundamentally re-architecting our approach to operational risk in an increasingly digital world. This is an investment in our future stability, trustworthiness, and competitive standing.
By embedding digital operational resilience into our corporate culture, our governance structures, and our daily operations, we will build a more robust and agile institution. The framework and roadmap outlined in this plan provide the tools to move beyond a defensive, compliance-oriented posture. Instead, we will proactively manage ICT risk, enhance our ability to withstand disruptions, and ultimately deliver more reliable and secure services to our clients. In doing so, we will satisfy our regulatory mandates while forging a powerful strategic advantage, positioning our institution for sustainable success and market leadership in the digital age.