In 2025, 10% of the entire cybersecurity industry was acquired in 400 deals. The platforms are feasting. The practitioners are starving. And the foreign military intelligence unit that built half the technology protecting your infrastructure just got $32 billion richer.
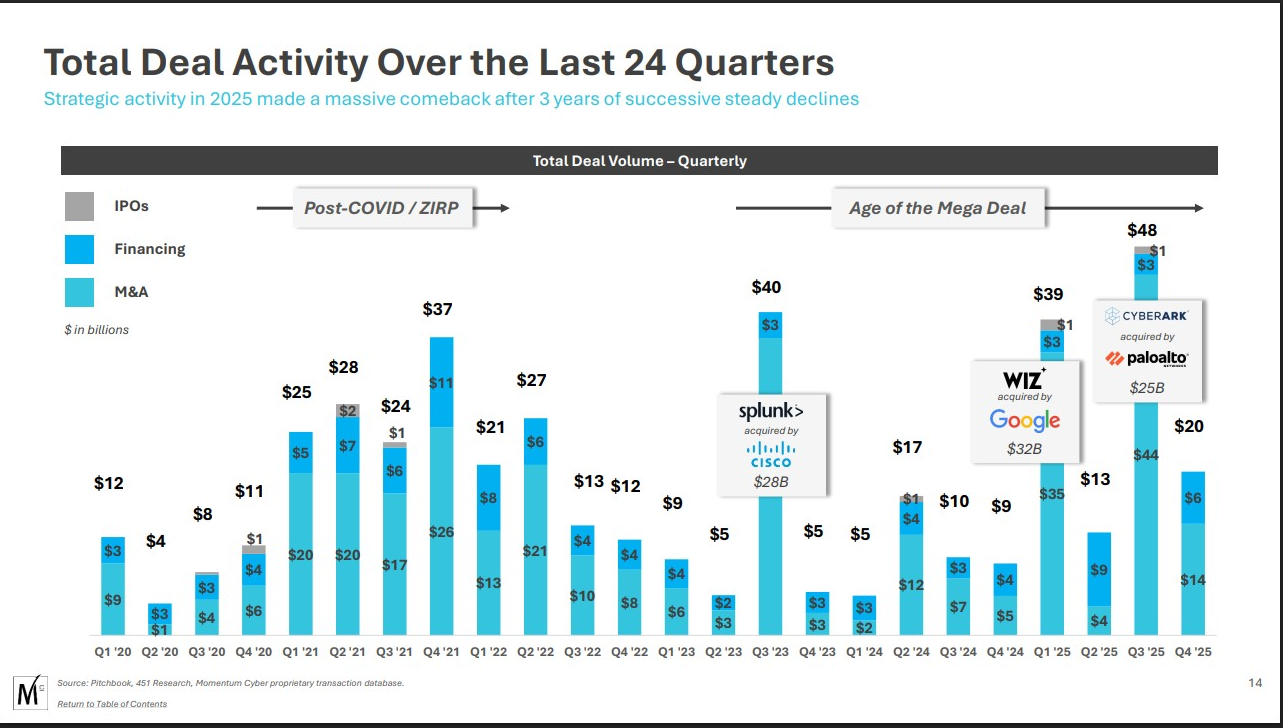
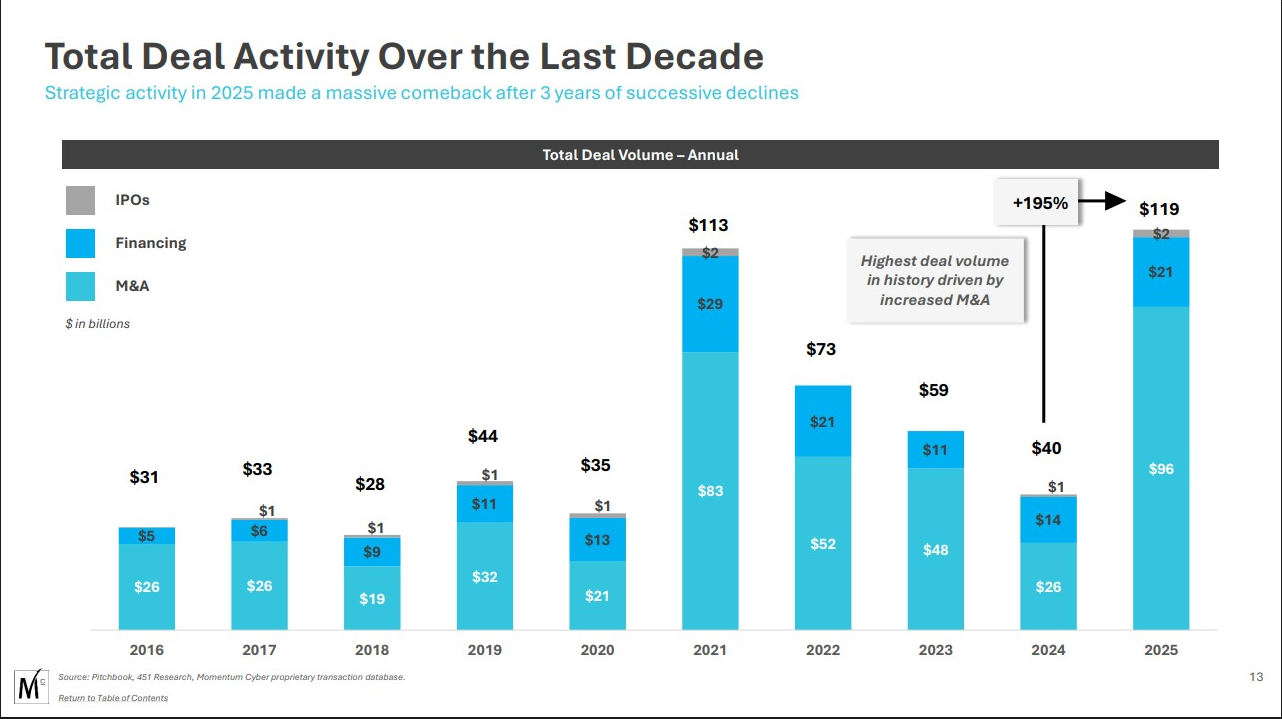
In January 2026, Momentum Cyber released its sixth annual Cybersecurity Almanac. The headline numbers read like a trophy case for investment bankers: $96 billion deployed across 400 transactions. A 294% year-over-year increase in deal value. The largest pure-play cybersecurity acquisition in history — Google swallowing Wiz for $32 billion. Q2 saw the highest quarterly transaction count ever recorded. Q3 broke the quarterly deal value record at $44.2 billion.
Richard Stiennon, one of the industry’s most respected analysts, called it what it is: a land grab.
He’s right. But from where I’m standing — someone who built a cybersecurity company to $1.79 million in revenue, watched it die, had intellectual property stolen during the fundraising process, and rebuilt from the ground up — the picture looks considerably darker than the M&A press releases suggest.
This isn’t a story about healthy market growth. It’s a story about what happens when the people writing the checks and the people doing the work occupy entirely different realities.
Follow the Money, Lose the People
Here is the central contradiction of cybersecurity in 2025, laid bare in two data points that should never coexist:
The industry deployed $96 billion in acquisitions. Strategic buyers — Palo Alto Networks, Google, CrowdStrike, Zscaler, Check Point, Accenture — captured 92% of all disclosed M&A value. Cloud-native and SaaS companies represented 59% of deal volume but absorbed 97% of all capital deployed. The platforms aren’t buying innovation. They’re buying market share, customer lists, and recurring revenue.
At the same time, 4.8 million cybersecurity positions remain unfilled globally. Sixty-seven percent of organizations report being short-staffed. Thirty-six percent of security teams experienced budget cuts. Thirty-nine percent faced hiring freezes. Twenty-six percent of respondents in ISC2’s 2025 Workforce Study anticipate more layoffs in the coming year. The number of active cybersecurity professionals worldwide grew by 0.1% since 2023. Not one percent. Zero-point-one.
So the industry found $96 billion to buy companies, but cannot find the budget to staff them.
Ben Rothke, a Senior Information Security Manager at Experian, captured the absurdity beneath Stiennon’s post with a single question: “With all that, why are they not hiring infosec pros?”
Nobody answered him. The answer is uncomfortable.
Momentum Cyber Releases 2025 Cybersecurity Almanac - Momentum Cyber
What $96 Billion Buys (And What It Doesn’t)
When Google acquires Wiz for $32 billion, it is not purchasing a solution to the cybersecurity skills gap. It is purchasing a customer base, a product architecture, and the ability to bundle cloud security into its existing platform sales motion. When Palo Alto Networks continues its platformization strategy through strategic acquisitions, it is reducing the number of vendors a CISO needs to manage — and simultaneously reducing the number of companies that employ cybersecurity professionals independently.
Every acquisition in that $96 billion figure has a human cost that doesn’t make it into the Almanac. Engineering teams get consolidated. Overlapping roles get eliminated. Regional sales teams get absorbed into the acquiring company’s go-to-market org. The tribal knowledge of the acquired company’s customer relationships gets transferred into a CRM and the people who built those relationships get severance packages.
Momentum Cyber’s own data tells the platformization story plainly. The most active M&A sectors were Security Services (126 deals) and Risk & Compliance (63 deals). These aren’t exotic technology categories. These are the operational backbone of how organizations actually get secured — the assessments, the consulting, the managed services, the compliance work. The platforms are not just buying technology. They’re buying the service layer and industrializing it.
CISO Marketplace | Cybersecurity Services, Deals & Resources for Security Leaders
IBM’s research found that organizations juggle an average of 83 different security solutions from 29 vendors. The consolidation pitch is seductive: reduce complexity, lower total cost of ownership, unify your data. Palo Alto’s CEO Nikesh Arora has made platformization his central thesis, arguing the industry can’t afford the luxury of fragmented, best-of-breed approaches when attacks move faster than detection.
He’s not wrong about the problem. But the solution being sold has consequences that nobody marketing consolidated platforms wants to discuss.
The View from the Wreckage
I know what consolidation looks like from the other side of the transaction because I’ve lived it — not as a buyer or a seller, but as collateral damage.
I built Vulsec, a cybersecurity assessment firm. We did the work. Penetration testing, vulnerability assessments, compliance evaluations. We reached $1.79 million in revenue. We had real clients with real security problems that we actually solved. Four hundred security assessments over the course of my career, across healthcare, energy, and Fortune 100 companies.
Then I tried to raise capital to scale.
What I encountered in the fundraising process wasn’t a meritocracy evaluating the strength of my technology or my track record. It was an extraction machine. I watched intellectual property from my pitch materials appear in competitors’ offerings. I sat through meetings where the interest wasn’t in funding my company but in understanding what I’d built well enough to replicate it or hand the insight to a portfolio company.
When COVID hit, the combination of revenue disruption and the failure to secure investment killed Vulsec. Not because the work wasn’t needed — it was. Not because the clients weren’t there — they were. But because the capital structures that supposedly exist to help cybersecurity companies scale were, in my experience, optimized for extraction rather than investment.
I rebuilt from nothing. I’ve been doing it from a converted van, running a content distribution network that now reaches millions of search impressions, publishing a daily podcast across 103 countries, building micro-tools, and continuing to do the hands-on consulting work that the platforms claim to automate. Fifteen years of cybersecurity experience doesn’t evaporate because a VC fund decided your company wasn’t the right fit for their portfolio’s exit timeline.
And from this vantage point — outside the conference circuit, outside the deal rooms, outside the self-congratulatory M&A announcements — the $96 billion land grab looks less like industry maturation and more like a hostile takeover of an entire profession.
The Vendor Risk Time Bomb
If you’re a CISO reading this, here’s where the Momentum Cyber data stops being an abstract market report and starts being an operational emergency.
Stiennon’s post ended with a warning: “Your vendor landscape is not stable. Act accordingly.”
Let me make that concrete. In 2025, 400 cybersecurity companies changed ownership. That means 400 companies whose products you may have evaluated, purchased, deployed, integrated, and built security workflows around are now controlled by different entities with different priorities, different product roadmaps, and different commitments to the features you depend on.
CISO Marketplace | Cybersecurity Services, Deals & Resources for Security Leaders
When a strategic buyer acquires a security vendor, the first thing that happens is product rationalization. Features that overlap with the buyer’s existing portfolio get deprecated. Integrations that served the acquired company’s ecosystem but conflict with the buyer’s platform strategy get deprioritized. Pricing models shift to favor the buyer’s bundle economics. Support teams get restructured. The product you bought is not the product you’ll have in eighteen months.
Forty percent of the M&A activity in 2025 was cross-border. That means your vendor’s data handling practices, regulatory obligations, and support infrastructure may have shifted jurisdictions without your awareness.
If your vendor risk management program doesn’t account for acquisition risk — if it evaluates vendors at the point of procurement and doesn’t continuously monitor for ownership changes — you’re not managing risk. You’re documenting the state of things at a moment that no longer exists.
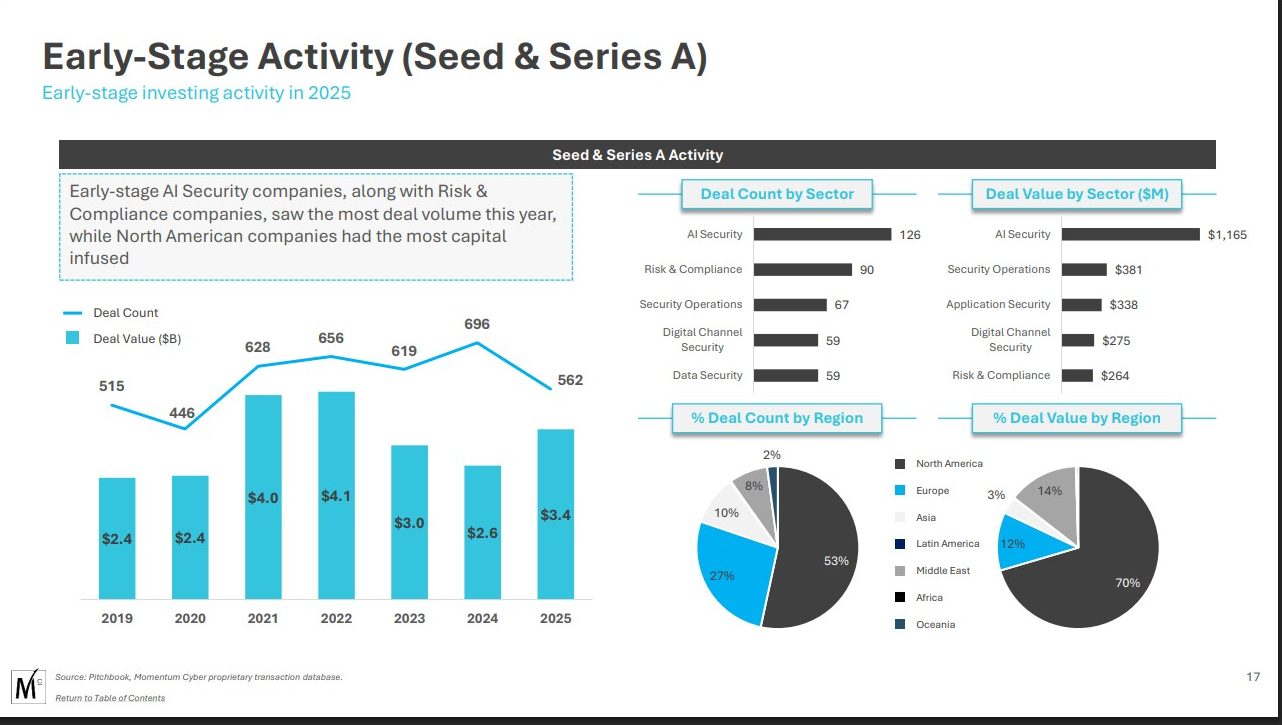
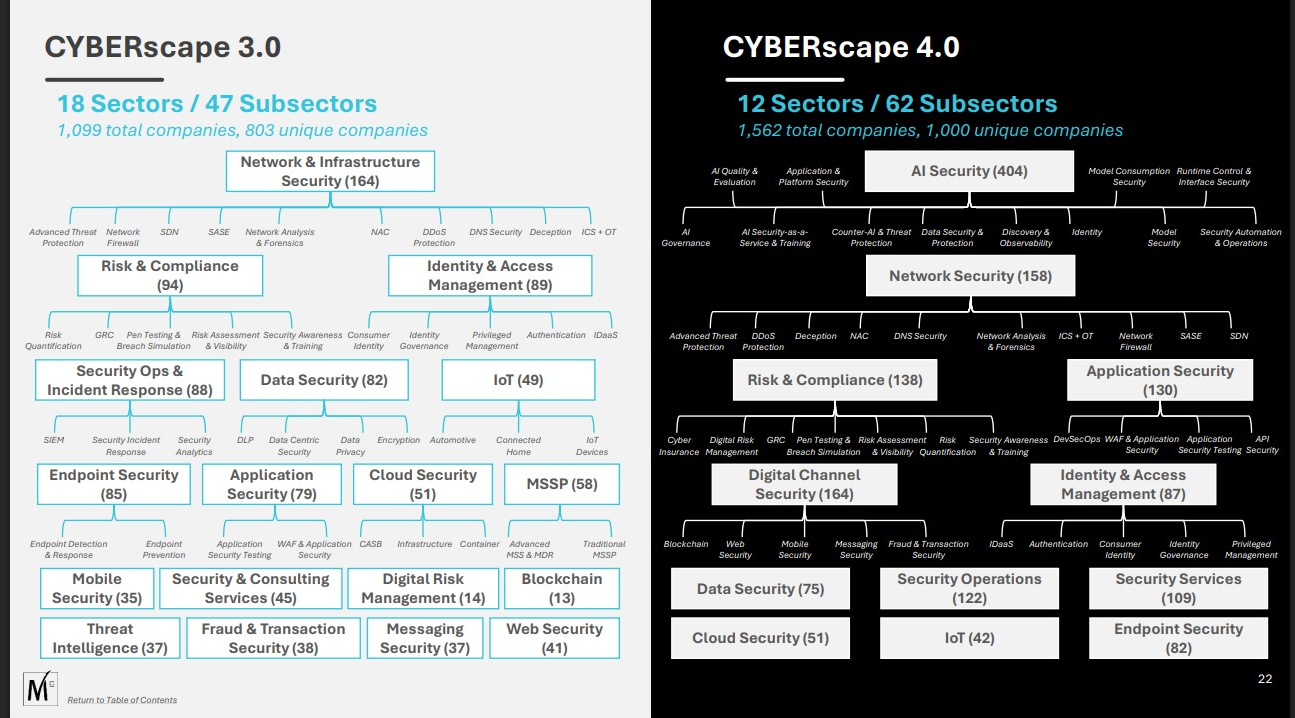
And here’s the part that should keep you up at night: the consolidation is accelerating. Momentum Cyber’s analysis suggests the pipeline for 2026 is already stacked. AI security is the fastest-forming subsector in cybersecurity history, with over 300 companies now mapped in that space alone. Those 300 companies are acquisition targets. Every single one of them.
The Two-Tier Market Nobody Wants to Acknowledge
Buried in the Almanac data is a structural shift that the industry press has largely ignored. Cybersecurity is splitting into two distinct markets.
The top tier consists of platform companies — the Palo Altos, the CrowdStrikes, the Googles, the Zscalers — that can acquire their way to comprehensive coverage. These companies trade at premium multiples, attract institutional capital, and set the terms of the market. They don’t just compete for customers. They compete for the right to define what cybersecurity means at an enterprise level.
The bottom tier is everyone else. The small firms doing penetration testing. The consultancies running compliance assessments. The solo practitioners and boutique teams that do the actual hands-on security work for the mid-market and below. These operators don’t show up in M&A deal flow because they’re not building for exit. They’re building for survival.
The workforce data confirms the bifurcation. ISC2’s 2025 study found that the largest organizations were hit hardest by economic measures — 32% reported layoffs, 46% experienced budget cuts, 49% faced hiring freezes. But the consolidation isn’t creating a rising tide. It’s creating a vacuum at the lower end of the market where small and mid-sized businesses face a 43% breach success rate when attacked, and the people who would protect them can’t find work or can’t get funded.
Cybersecurity financing did reach $20.7 billion across 820 deals in 2025 — up 52% from the prior year. But the median Series C+ deal size jumped from $50 million to over $80 million. Capital isn’t being distributed. It’s being concentrated. AI security and cloud infrastructure are pulling almost all of it. If you’re not building in those categories, the fundraising environment isn’t tight — it’s nonexistent.
The Geography Nobody Wants to Talk About
There is a dimension to this consolidation that the cybersecurity press treats as untouchable, and it may be the most consequential risk of all: where the technology originates, who built it, where the AI models are trained, and what jurisdiction governs the people with root access to your infrastructure.
Forty percent of all cybersecurity M&A activity in 2025 was cross-border. Momentum Cyber’s own data identifies Israel as the single most significant source of innovative cybersecurity companies being acquired. And the numbers behind that statement are not subtle.
Israeli cybersecurity startups raised a record $4.4 billion across 130 funding rounds in 2025. Israeli cyber companies attracted 38% of all tech investment flowing into the country despite comprising only 7% of its tech ecosystem. Israeli cybersecurity funding in 2024 was equivalent to 40% of the entire U.S. cybersecurity funding market. Seven of the world’s top ten cybersecurity companies maintain R&D centers in Israel. Half of the world’s cybersecurity unicorns were founded by Israelis. Over 500 Israeli cybersecurity companies are actively developing technologies spanning cloud security, endpoint protection, identity management, AI-driven threat detection, and industrial system safeguards.
Cybersecurity Consolidation 2023-2025: Major M&A Deals and Market Dynamics
The companies being acquired in the largest transactions of the consolidation wave read like a roster of Israeli intelligence alumni. Wiz, acquired by Google for $32 billion, was founded by four veterans of Unit 8200, the Israeli Defense Forces’ signals intelligence division — widely described as Israel’s equivalent of the NSA. CyberArk, acquired by Palo Alto Networks for $25 billion, was founded by Unit 8200 alumni. Check Point, Palo Alto Networks itself (co-founded by Nir Zuk, a Unit 8200 veteran), Armis, Cybereason, Axonius — the list of cybersecurity companies with direct lineage to Israeli military intelligence is extensive and growing.
Palo Alto Networks alone has made nearly half of its major acquisitions from companies with Israeli intelligence origins — LightCyber, Dig Security, Talon Cybersecurity, Secdo, Bridgecrew, Cyvera, Twistlock, and Puresec — all founded or led by veterans of Unit 8200 or related IDF cyber units.
This isn’t about questioning the technical talent. Unit 8200 produces extraordinary engineers. The technology coming out of Israeli cybersecurity firms is often genuinely best-in-class. That’s not the issue.
The issue is this: when your organization deploys an endpoint detection platform, a cloud security posture management tool, a privileged access management system, or an identity governance solution, you are granting that technology — and by extension, the people who built and maintain it — access to your network traffic, your credentials, your root-level systems, and your data. You are trusting that the AI models making security decisions about your infrastructure were trained with your interests in mind and that the humans who can access those systems are accountable to your legal and regulatory framework.
The AI Data Center Gold Rush: When $1+ Trillion in Investments Meets Community Resistance
The Kaspersky precedent is instructive — and the timeline matters. In 2017, the Department of Homeland Security ordered federal agencies to remove Kaspersky Lab products from government systems over concerns about the company’s ties to Russian intelligence. Congress codified the ban into the 2018 National Defense Authorization Act. In 2019, the Federal Acquisition Regulation Council extended the prohibition to all government contractors. Then in June 2024, the Biden administration banned all Kaspersky sales to U.S. consumers and businesses entirely, with a hard cutoff of September 29, 2024 — no sales, no updates, no support. A seven-year escalation from federal concern to total prohibition.
The rationale was never that Kaspersky was proven to be a spying tool. It was that the structural relationship between the company, its personnel, and a foreign government’s intelligence apparatus created an unacceptable risk profile. As Commerce Secretary Gina Raimondo stated: “Russia has shown it has the capacity and the intent to exploit Russian companies like Kaspersky to collect and weaponize the personal information of Americans.”
Now apply that same logic to the current cybersecurity landscape. Replace “Russian company” with “company founded and staffed by veterans of a foreign military intelligence unit.” Replace “Russian government’s offensive cyber capabilities” with the documented capabilities of Unit 8200. The structural risk argument is identical. The policy response is nonexistent.
Axonius, a cybersecurity asset management platform founded by Unit 8200 veterans, helps manage and monitor devices across more than 70 U.S. federal agencies, including the Pentagon and the Department of Homeland Security. In 2025, Microsoft terminated Unit 8200’s access to parts of its Azure cloud infrastructure after revelations that the unit had been storing thousands of terabytes of intercepted Palestinian phone calls on Microsoft servers in Europe — a program designed to analyze millions of calls daily.
CISO Marketplace | Cybersecurity Services, Deals & Resources for Security Leaders
The cybersecurity industry that is supposed to protect enterprise and government infrastructure is increasingly built, developed, and maintained by veterans of a foreign military intelligence unit that has documented involvement in mass surveillance operations, AI-driven targeting systems, and the creation of technologies used for population monitoring.
None of this means every Israeli cybersecurity product is compromised. That would be a reckless claim. But it does mean that the vendor risk conversation needs to include questions that CISOs have been trained to avoid asking:
Where is the R&D team located? What jurisdiction governs the engineers who have access to your deployment? Where are the AI models that power your security tools trained, and on what data? What is the military or intelligence background of the founding team and current engineering leadership? If the geopolitical landscape shifts — sanctions, conflicts, diplomatic realignments — what happens to your security vendor’s ability or willingness to serve your organization? Who actually has access to the telemetry your security tools collect?
Vendor Risk Management Tool | Third-Party Risk Assessment
If you asked these questions about a Russian or Chinese cybersecurity vendor, nobody would blink. The fact that asking them about Israeli vendors is treated as controversial tells you more about the industry’s political sensitivities than about the actual risk calculus.
Your vendor risk program should be jurisdiction-agnostic. Risk is risk. And when one country’s military intelligence apparatus has produced the founders, engineers, and leadership of a disproportionate share of the technology protecting your most sensitive systems, that is a concentration risk that belongs on your risk register — regardless of the ally relationship between governments.
What Needs to Change
The Momentum Cyber Almanac is a valuable document. It quantifies what’s happening. But what it doesn’t do — what no investment banking report ever does — is ask who this benefits beyond the parties to the transaction.
The cybersecurity industry has a practitioner problem that $96 billion in M&A activity not only failed to solve but actively made worse. Every acquisition that eliminates redundant teams reduces the pool of employed security professionals. Every platformization play that bundles security into a suite sale reduces the number of independent vendors competing on capability. Every mega-round that concentrates capital in AI security and cloud platforms dries up the funding environment for assessment firms, consulting shops, and the operational security work that actually reduces risk at the organizational level.
It has a sovereignty problem that nobody in the vendor community wants to acknowledge. The companies securing your infrastructure are increasingly controlled by, built by, and maintained by personnel from a single foreign military intelligence apparatus. The concentration risk is real, measurable, and absent from virtually every vendor risk framework in use today.
And it has an honesty problem. The industry celebrates $96 billion in deal flow while 4.8 million security positions go unfilled, budgets get cut, practitioners get laid off, and CISOs are told to consolidate onto platforms whose ownership, jurisdiction, and data practices can change with the next acquisition.
If the industry spent even a fraction of that $96 billion on the humans who do the work — on hiring, on training, on funding the operational layer that platforms can’t automate — the workforce gap would start to close. If vendor risk programs asked the hard questions about technology provenance, jurisdiction, and intelligence community lineage, organizations would make more informed decisions about who they trust with root access.
Instead, we get another year of record M&A, another Almanac, and another round of congratulations from the people who profit from transactions while the people who do the work update their resumes.
Your vendor landscape is not stable. Your technology supply chain has geographic and geopolitical concentration risks that aren’t on your risk register. Neither is your staffing plan, your risk model, or the assumption that the company securing your cloud infrastructure today will exist in its current form — or serve your interests — a year from now.
Act accordingly.
Cybersecurity M&A Update Report 2025 | Complete Year-End Analysis
*Andrew has spent 15 years in offensive security, completed over 400 security assessments across healthcare, energy, and Fortune 100 companies, and built the CISO Marketplace ecosystem to provide independent cybersecurity guidance outside the consolidation machine. He publishes daily at compliancehub.wiki and produces a **cybersecurity podcast *reaching 103 countries.



